Penetration Test - Identify and Fix Vulnerabilities
A successful attack on your IT infrastructure can have serious consequences: data loss, damage to your image, high restoration costs. A professionally conducted pentest (penetration test) helps you identify and eliminate precisely these risks at an early stage. Turingpoint offers you practical, manual penetration tests that meet the highest standards – individually tailored by a BSI-certified IT security service provider
Effective Solution for High IT Security
What is a Pentest?
A Pentest is a targeted security test in which experienced IT security experts carry out simulated attacks on your systems. The goal is to identify, evaluate, and provide specific recommendations for securing vulnerabilities in web applications, mobile apps, or infrastructures. Recognized standards such as OWASP, BSI, OSSTMM or PTES are used.
Reasons for a Pen-Test
Why is a Pentest Useful?
A Pentest provides you with:
- Early detection of security vulnerabilities before attackers can exploit them
- Minimization of IT risks and potential downtimes
- Support in complying with security guidelines (e.g. ISO 27001, IT-Basic Protection, ISMS)
- Transparency about your Cyber Resilience
- Cost savings through targeted investments in security-critical areas

Process Steps of a Successful Penetration Test
This is How a Pentest Works at turingpoint
A professional pentest is a multi-stage process. Our experts guide you transparently through each phase:
- Management Summary
- Overview of vulnerabilities incl. CVSS rating
- Recommendations for remediation
- Business Risk Analysis
Kick-off & Goal Definition
In a joint discussion, the framework conditions are defined: test objectives, access points, contacts, and escalation paths.
Information Gathering & Analysis
Our pentesters deliberately gather technical information to identify potential attack vectors.
Manual Vulnerability Analysis
Through manual testing - supplemented by our own and commercial tools - we check your systems for vulnerabilities. In doing so, we distinguish false positives from real risks.
Exploitation
Real exploitation of vulnerabilities to validate criticality. Depending on the target system, individual exploits are also used.
Reporting
You will receive a comprehensive report including:
Final Discussion & Re-examination
We discuss the results with you in detail. A one-time re-examination is included free of charge.
Penetration Testing Abstraction Levels for All Technologies
Our Types of Tests at a Glance
We also have experience with modern Cloud platforms such as AWS, Google Cloud and Microsoft Azure. Furthermore, we classify the following types of tests:
Web Applications
Testing for common vulnerabilities in web technologies and APIs (e.g. XSS, SQLi, authentication errors).
Mobile Apps
Analysis of communication interfaces and app-internal vulnerabilities. Always in conjunction with backend systems.
Infrastructures
Testing of critical systems such as servers, VPN, Firewalls or Active Directory - also suitable for KRITIS companies.
Test Methods Compared
Pentest Methods: Black Box, White Box & Grey Box
Depending on the objectives and available information, we use different testing methods. The choice of method influences the scope, depth, and type of vulnerabilities identified.
No Prior Information
Black Box Pentest
In a Black Box Pentest, the testing team receives no internal information about the target system — just like a real external attacker. This method simulates realistic attack scenarios and reveals which vulnerabilities an attacker could exploit from the outside.
- Realistic simulation of an external attacker
- Identification of vulnerabilities without insider knowledge
- Ideal for testing the external attack surface

Full Access and Documentation
White Box Pentest
In a White Box Pentest, our testers receive full access to source code, architecture documentation, and system configurations. This enables the most thorough analysis and uncovers hidden vulnerabilities that would remain undetected in a Black Box test.
- Deepest analysis with source code access
- Identification of logic flaws and hidden vulnerabilities
- Most efficient method for maximum coverage

Partial Information
Grey Box Pentest
The Grey Box Pentest combines elements of both approaches: The testing team receives limited information such as user accounts, API documentation, or network diagrams. This simulates the scenario of an authenticated user or internal employee.
- Simulation of an authenticated user or insider
- Optimal balance between realism and test depth
- Most common method in practice — recommended for most projects

Attack from the Outside
External Pentest
An external pentest examines your publicly accessible systems from the perspective of an internet-based attacker. Web servers, mail servers, VPN gateways, and cloud services are systematically tested for vulnerabilities. This is the most important first step in securing your IT infrastructure.
- Testing all publicly accessible systems and services
- Identification of misconfigurations and exposed services
- Recommended as the first step for any organization

Expertise in Cyber Security
Your Advantages with a Pentest from turingpoint
- Manual execution by experienced Security Engineers
- BSI-certified IT security service provider in the field of IS penetration testing
- Recognized Standards (OWASP Testing Guide, BSI, NIST, PTES, among others)
- Certified Reporting & Customer Certificate upon request
- Free re-examination included
- Can be conducted remotely or on-site
- External ISO-27001 certification according to IT basic protection available

Penetration Tests by turingpoint are Handmade!
Automated vulnerability scanners cannot replace comprehensive penetration tests. It would be negligent to believe that a vulnerability scan offers a good level of security or protection against a real attacker! We offer Remote or on-site execution.
Optionally, we can additionally check your systems through a Darknet Intelligence Assessment.
- Prices
The cost of a pentest depends on the scope, complexity, and target systems. Our pentest service may be eligible for funding. We would be happy to provide you with a personalized quote.
- 5 Reasons Why You Should Conduct Penetration Tests
The safest way to measure your own security level is to investigate how it can be hacked. A pentest offers the opportunity to test the resilience (Cyber Resilience) of your system against external and internal hacking attempts.
- State of IT Security in Germany 2024
Even though it may sound counterintuitive, spending money on pentests will actually save your company a considerable amount of money. Without penetration tests as a guide, it would be necessary to spend more money on a wider range of aspects. BSI Situation Report
- Annual Number of Data Losses and Disclosed Data Sets
Penetration tests play a crucial role in protecting your company and its valuable assets from potential intruders. However, the benefits of a pentest go far beyond network and data security. Source Statista
Range of Services for Cyber Security
Additional Meaningful Services within the Scope of an IT Security Audit
- Cloud Security
Due to the increasing complexity of cloud infrastructures, many services are incorrectly configured. We help you identify and eliminate misconfigurations and their impacts.
- Phishing Simulation
A spear-phishing simulation is used to enhance the detection capabilities of your employees. We help you to raise awareness among your staff and thus strengthen the last line of defense.
- Static Code Analysis
Static code analysis, also known as source code analysis, is typically conducted as part of a code review and takes place during the implementation phase of a Security Development Lifecycle (SDL).
- Red Teaming
Red Teaming is used to test an organization's detection and response capabilities. Our Red Team attempts to access sensitive information in every conceivable way and as undetected as possible.
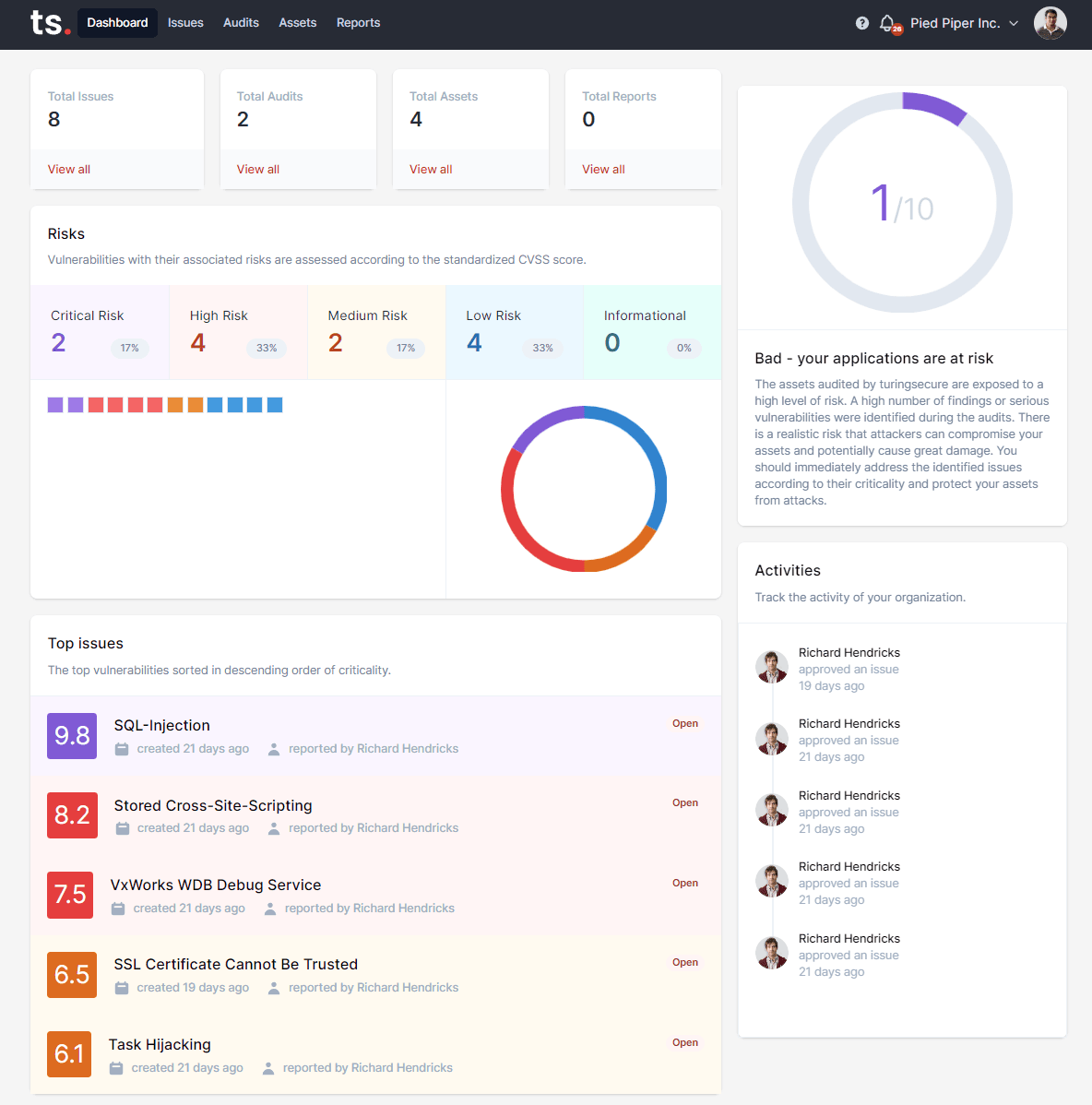
Penetration Testing as a Service (PTaaS)
Penetration Testing on the turingsecure platform.
We offer comprehensive vulnerability management for customers, partners, penetration testers, and IT security consultants. Use our software products to also get the best technology and reporting tools on the market.
Application-level security measures
Comprehensive Solutions for Your Application Security
With our extensive and intuitive Pentest platform turingsecure, you can now map the entire security process of your applications. This platform was programmed with the Security Library kodado.
- Continuous Application Security Testing
Continuous Security Application Testing (CAST) ensures that applications are examined for vulnerabilities in a regulated cycle. Our methodology allows for direct integration into the agile development process, thereby enabling a high level of continuous security.
- On-Demand Penetration Testing
Penetration tests of applications are scaled as needed to meet more complex requirements. For a demanding application, a quick and manual penetration test can be conducted to identify vulnerabilities in your application's business logic.
- Vulnerability Management & Reporting
turingsecure can classify, prioritize, and identify all vulnerabilities related to application security. All findings are graphically processed for a better insight. A management summary, vulnerability details, and remediation steps can be exported in PDF and machine format.
Linkable on your website
Certification with Seal
We have developed an effective and comprehensive format for verifiable security that can be directly integrated into your website. This certificate demonstrates to third parties such as customers or insurance companies a high level of security, data protection, and an awareness of IT security.
The certificates we issue demonstrate a high level of IT security at a given time after a standard or individual test modules. Depending on the Assessment, different test guidelines are chosen and evaluated.

Our E-Book
eBook: Finding the Right Pentest Provider
Searching for the right provider for pentests can be a problematic process, especially for those who are not familiar with IT security. What do I need? How do I know who can demonstrate sufficient technical expertise? How do I identify unqualified pentest providers? How do I recognize good reputation and competence? What should the documentation look like?
In this eBook, we provide you with 6 questions you should ask potential service providers for your next penetration test. You will know what to look for when selecting a provider, how to compare the different offers, and ultimately make the best choice for your specific requirements.

Frequently Asked Questions
FAQ: Frequently Asked Questions About Pentest
We have selected and answered the most frequently asked questions for you.
Current Information
Recent Blog Articles
Our employees regularly publish articles on the subject of IT security
Contact
Curious? Convinced? Interested?
Schedule a no-obligation initial consultation with one of our sales representatives. Use the following link to select an appointment:













