Cost and Pricing for a Pentest
What costs should be considered for a pentest? The response depends on several factors, including the complexity of the organization to be evaluated.

Penetration testing is a critical activity for securing an organization's information resources and IT infrastructure, including communication networks, software solutions, endpoints (workstation PCs and laptops running Windows and Linux, mobile apps), servers, and cloud solutions such as AWS infrastructure.
Today, penetration testing is a mandatory requirement for hospitals, financial institutions, telecommunication providers, public institutions and authorities, as well as the service industry in general. While demand for pentesting services has grown, stakeholders still face challenges in establishing a fair pricing structure that works for both the pentesting provider and the client organization.
What Costs Should Be Considered for a Pentest?
This question typically arises when negotiating the cost of an IT pentest. The answer depends on several factors, including the complexity of the organization, server systems, and applications to be assessed, the analyst's experience, the cost of scanning tools used by the pentest vendor including license fees, the scope of the test, any remediation actions based on the test results, and the retest. Specialized requirements can also increase costs, such as SAP pentesting, protocol or hardware analysis, or a specific testing framework like PCI DSS.
The following section outlines the key factors that influence pentest pricing. As a client, it is often time-consuming and difficult to determine what a pentest should cost. As a pentest service provider, on the other hand, you want to avoid quoting prices that might alarm a customer or push them to seek alternatives.
The most important factor in determining pentest costs is the complexity of the client organization and its network environment. Organizations with complex, distributed networks, numerous network devices, multi-layered API endpoints, and sophisticated application software naturally have more potential attack vectors. Their pricing will be significantly higher than for organizations with simpler infrastructure, fewer mobile apps, and more straightforward frontend and backend systems.
Additionally, the scanning tools used by the service provider are part of the overall cost, as the fees must cover tool acquisition and license expenses. Otherwise, it would not be economically viable to pay for software licenses without being able to recoup those costs through the work performed.
The IT security provider's experience and the profile of its customer base also play a role. If the provider has won high-profile clients and handles a large volume of engagements, it will typically charge a higher price.
Another factor influencing the final fee is the test scope, which is often defined by the client organization. The scope has a significant impact on the final quote, as the testing provider must align its billing with the agreed-upon parameters. However, it is risky to let cost concerns drive a reduction in scope, as an overly narrow focus leaves little room for identifying actual vulnerabilities and control gaps in the operating environment.
Pentest Costs in Relation to Cost-Effectiveness
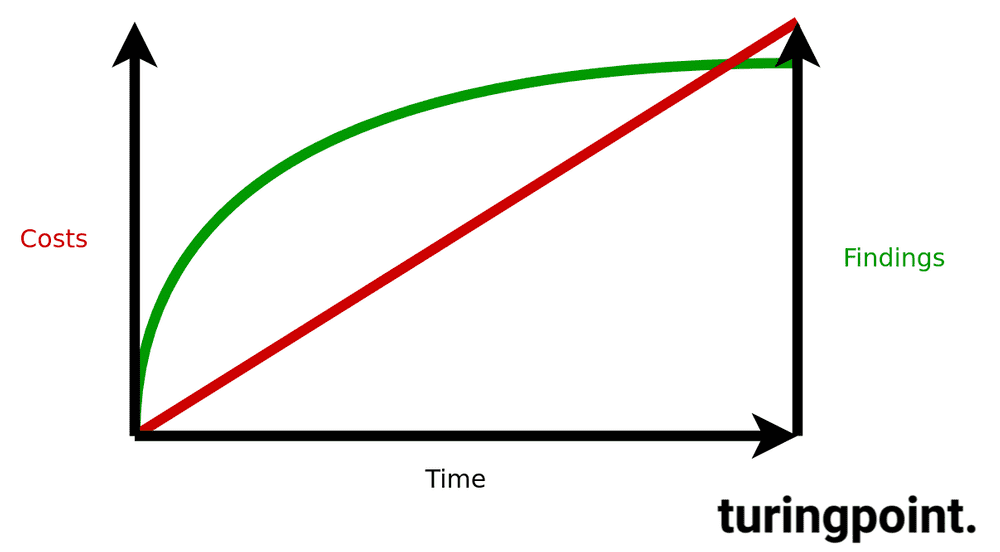
IT security is always a matter of trade-offs, so a cost-efficient approach toward an optimum is essential. As a general rule, the longer pentesters examine the infrastructure, mobile apps, or web applications, the more meaningful the results.
Penetration tests are snapshots that can become outdated within as little as one week. This should also be factored in, as future tests can be performed incrementally to reduce costs. Regular and event-driven automated pentesting can help maintain a basic, though limited, security standard and maturity level.
What Are the Average Costs for a Pentest Project?
The answer depends largely on the factors outlined above. For simple or less complex networks and software, you can expect fees in the range of 4,500 to 6,000 euros. For a moderately complex organization with a diverse system architecture, a price between 10,000 and 15,000 euros is typical. For large organizations with highly complex networks, distributed systems, and web services, budgets of up to 100,000 euros may be required -- which is not disproportionate given the risks and consequences of a successful attack.
Organizations should regularly assess the value of their business data and IT infrastructure and weigh it against the risk and consequences of a successful attack. This allows for a well-founded assessment of whether the cost of a security evaluation is worthwhile. Keep in mind that services offered at conspicuously low prices may not deliver meaningful results. Vulnerability assessment through penetration testing is an essential measure for any organization that processes personal or financial data under legal or regulatory requirements.
For any organization planning an IT pentest, it is therefore important to consider not only the cost but also the criticality of vulnerabilities in relation to its security and information assets. Since existing attack vectors increase the likelihood of a successful breach, it is essential to keep your information resources and operating environment free from vulnerabilities that attackers could exploit. Hackers -- whether internal or external -- can cause significant damage if they find even the slightest opportunity. The least you can do is reduce your attack surface as much as possible through appropriate preventive measures.
Variable Pentest Costs
Variable costs are costs that vary depending on time, additional services or special methods.
1. Scope and Duration of the Engagement
The test scope directly impacts the time required for completion. Factors that influence duration and subsequent costs include the size of the website, the number of tenants to be tested, the range of functionality, associated APIs or web services, and the complexity of the PC, server, or cloud infrastructure.
2. Tools
Every pentester takes a different approach to conducting their test. Some use more expensive tools than others, which can increase the price. However, high-quality tools can shorten test duration and deliver better results.
3. Test Concepts
Depending on the information available, white-box, grey-box, or black-box tests are performed. Gray-box tests encompass all test types that fall between white-box and black-box tests. The analyst receives some information, typically only login credentials. All other information must be independently analyzed. This test type offers a practical compromise in terms of the number of test cases, cost, speed, and scope. Gray-box tests are the most common type of test in the security industry.
4. Experience of the Pentester
Analysts with more experience are typically more expensive. Remember: you get what you pay for. Be cautious of pentest vendors whose prices seem too good to be true, as they often do not deliver thorough work. It is advisable to look for penetration testers who hold recognized certifications such as OSCP, CISSP, GIAC, or CEH.
5. Retest
All pentests carried out by the contractor should include a one-time free retest, during which previously identified vulnerabilities are re-examined. This retest validates whether the client's remediation measures have achieved the desired effect.
So What Are the Costs?
Each project is tailored to the organization being tested. As a general guide, an automated test with comprehensive results analysis and a detailed list of security recommendations falls within the average cost range described above. Daily rates vary between vendors and should be viewed critically if set conspicuously low. Scope and duration of the engagement, tools, test concepts, pentester experience, and the retest are the key levers for tailoring the engagement to your needs.
In most cases, the decisive factor is how much manual work is performed that cannot be replaced by automation. Even at higher costs, there is no better way to test your security systems.