Cloud Pentest - Security Audit for Cloud Structures
Due to the increasing complexity of cloud infrastructures, many services are incorrectly configured. We help you identify and eliminate misconfigurations and their impact on cloud security.
Definition and Explanation
What is a Cloud Security Assessment?
A Cloud Pentest is a targeted security review of cloud infrastructures. Experts simulate attacks to identify vulnerabilities early on. The goal is to ensure the security of data and applications in the cloud.
The effectiveness of a Cloud Pentest is evaluated based on several criteria that concern both the depth and quality of the test. A central aspect is the realistic representation of attack paths and the comprehensive coverage of all relevant cloud resources, including configurations, access rights, and interfaces. A Cloud Pentest is particularly effective when it considers the entire attack surface of the cloud environment and does not just test individual services in isolation.
In the long term, the effectiveness of a Cloud Pentest is also measured by how sustainably the security gaps are closed and how continuously the cloud environment is monitored and tested. Regular, recurring pentests and integration into the DevOps process (Continuous Validation) increase cloud security and ensure that new vulnerabilities are identified promptly.

Procedure
How do you Check the IT Security of a Cloud?
A Cloud Pentest consists of several phases. First, planning and goal definition take place. After that, information is gathered and vulnerabilities are identified. Subsequently, attacks are simulated and the results are documented.
After the test, companies receive a detailed report. It contains all the vulnerabilities found and specific recommendations for action. The implementation of the measures is accompanied by the experts.
Security and Penetration Testing
Cloud Penetration Testing for Enhanced Cyber Security
Penetration testing for cloud configurations is planned, conducted, and evaluated by our specially trained security engineers according to recognized standards of cyber security.
- Comprehensive Report Format
Our report is created according to recognized standards and includes, among other things, a management summary, a vulnerability overview, details on vulnerabilities, and remediation steps. The evaluation of the findings is based on the CVSS 3.0 standard.
- Certification as Proof for Your Customers
Use our comprehensive security certificate to demonstrate the high level of security of your applications and infrastructures to customers. A successful accreditation is preceded by a cloud assessment or penetration test.
- Execution according to recognized standards
We offer the following testing standards: OWASP and CIS Benchmark. Depending on the information base, we conduct White-, Gray-, or Black-Box tests.

Cyber Security in the Cloud
Boutique Consulting with Expertise in Cloud Cyber Security Assessments
We offer all services in various complexities and recognized standards.
- Identity and Access Management
The analysis of permissions for privilege escalation paths and the examination of incorrectly configured roles as well as unauthorized access attempts.
- CIS Benchmark
CIS Benchmarks are among the best practices that can help you securely configure a target system. They assist you in securing your IT systems, networks, software, and cloud infrastructure.
- OWASP Cloud Testing Top 10
With the OWASP Cloud-Native Application Security Top 10, we test companies that want to securely implement cloud-native applications. This guide contains the most important attack vectors for the cloud.

Process Steps of Cloud Security
Methods for Cloud Security
The assessment we conduct is an agile process and is carried out in close consultation with the customer.
Kick-off
During a joint kick-off meeting, the conditions to be tested are specified, necessary user accounts and access paths are coordinated, contacts and escalation paths are defined, and the pentest is planned in detail together.
Manual & Automated Research
Our security engineers strive to gather as much information as possible. Based on this information, analysis strategies are developed to identify potential attack vectors. These attack vectors are then extensively tested for vulnerabilities.
Manual Exploitation
Here, the identified vulnerabilities are exploited in an attempt to gain access to the target systems. Depending on the respective service or technical environment, our pentester writes new exploits or uses existing ones. Potential vulnerabilities may turn out to be false positives here. Only verified vulnerabilities are included in the final report and classified according to their criticality using CVSS 3.0.
Report
We have developed a comprehensive report format that provides optimal insight into our work and its results. This consists of a business risk analysis, management summary, and an extensive test and vulnerability description. The criticality of the vulnerabilities and recommendations for action are described in detail in this report.
Final Discussion & Certification (Optional)
In the final discussion, all critical points in the report are discussed and all questions are clarified. Finally, we are happy to present you with a certificate as proof for your customers.
Remediation (Optional)
Once the analysis is complete, you will proceed with the remediation of the identified vulnerabilities. Our evaluations provide you with detailed recommendations about each vulnerability. If needed, our security engineers can provide extensive assistance for the remediation.
Free Re-examination (Optional)
We are happy to re-examine the security weaknesses to ensure that the defense mechanisms have been implemented correctly. It is important to us that our recommendations are implemented, which is why this process activity is always free of charge.
Levels of Abstraction
Depth of the Cyber Security Assessment
Cloud Configuration Management
The various configurations in the form of identity and user rights differ greatly from traditional infrastructure. Our approaches are specifically tailored to these needs and effectively identify configuration and implementation errors.
Self-managed Infrastructure
We help you to review your networks and protect your assets. From mail servers to firewalls testing - we find the vulnerabilities in your systems!
Compliance Checks of the Self-Managed Infrastructure
In IT security, there are many guidelines that must be adhered to. Non-compliance usually does not represent a weakness in the traditional sense. We review existing compliance guidelines or adapt our security recommendations for your company.
The 3 Most Common Providers
Our Security Review in the Field of Cloud Security Assessment
We offer a cloud security audit for the following cloud providers.
Amazon Web Services
One of the strongest features of AWS is the immense flexibility offered to the user when setting up the environment. This flexibility is great, but it also poses a significant security problem. A pentest of the AWS cloud infrastructure can identify these security issues.
Google Cloud Platform
The GCP provides a shared responsibility model, where the customer is responsible for security, such as server configuration and the implementations granted with privileges in the environment. We identify faulty configurations in GCP Pentesting.
Microsoft Azure
Azure is equipped with a series of security precautions for experienced users. While this is a good start, it is the responsibility of each user to maintain its stability and security. With an Azure Pentest, we check the security of the cloud provider's configuration.
Cloud Penetration Testing
Objectives, Benefits and Legal Framework
A Cloud Penetration Test systematically identifies security vulnerabilities in cloud environments and provides specific recommendations for improving cloud security. This takes into account legal aspects, scoping, and typical vulnerabilities.
- Objective and Benefits of a Cloud Pentest
A Cloud Pentest helps to systematically identify security gaps. Companies receive concrete recommendations for improving their Cloud Security. This effectively prevents data loss and attacks.
- Legal and organizational framework conditions
Before a cloud pentest, legal questions need to be clarified. The consent of the cloud provider is often required. Data protection and compliance policies must also be observed.
- Scoping: Scope and Limitation of the Cloud Pentest
During the scoping process, it is determined which systems and services will be tested. Clear agreements prevent misunderstandings and ensure an efficient test. The goal is a tailor-made scope of examination.
- Typical Vulnerabilities and Threats in Cloud Environments
Common vulnerabilities include faulty access rights, insecure interfaces, and incorrectly configured services. Outdated software and weak passwords are also risk factors. Attackers deliberately exploit such gaps.
Range of Services for Cyber Security
Additional meaningful services within the scope of an IT security audit
- Penetration Test
Penetration tests are simulated attacks from external or internal sources to determine the security of web applications, apps, networks, and infrastructures and to uncover any vulnerabilities.
- Phishing Simulation
A spear-phishing simulation is used to enhance the detection capabilities of your employees. We help you to raise awareness among your employees and thus strengthen the last line of defense.
- Static Code Analysis
Static code analysis, also known as source code analysis, is typically performed as part of a code review and takes place during the implementation phase of a Security Development Lifecycle (SDL).
- Red Teaming
Red Teaming is used to test an organization's detection and response capabilities. Our Red Team attempts to access sensitive information in every conceivable way and as undetected as possible.
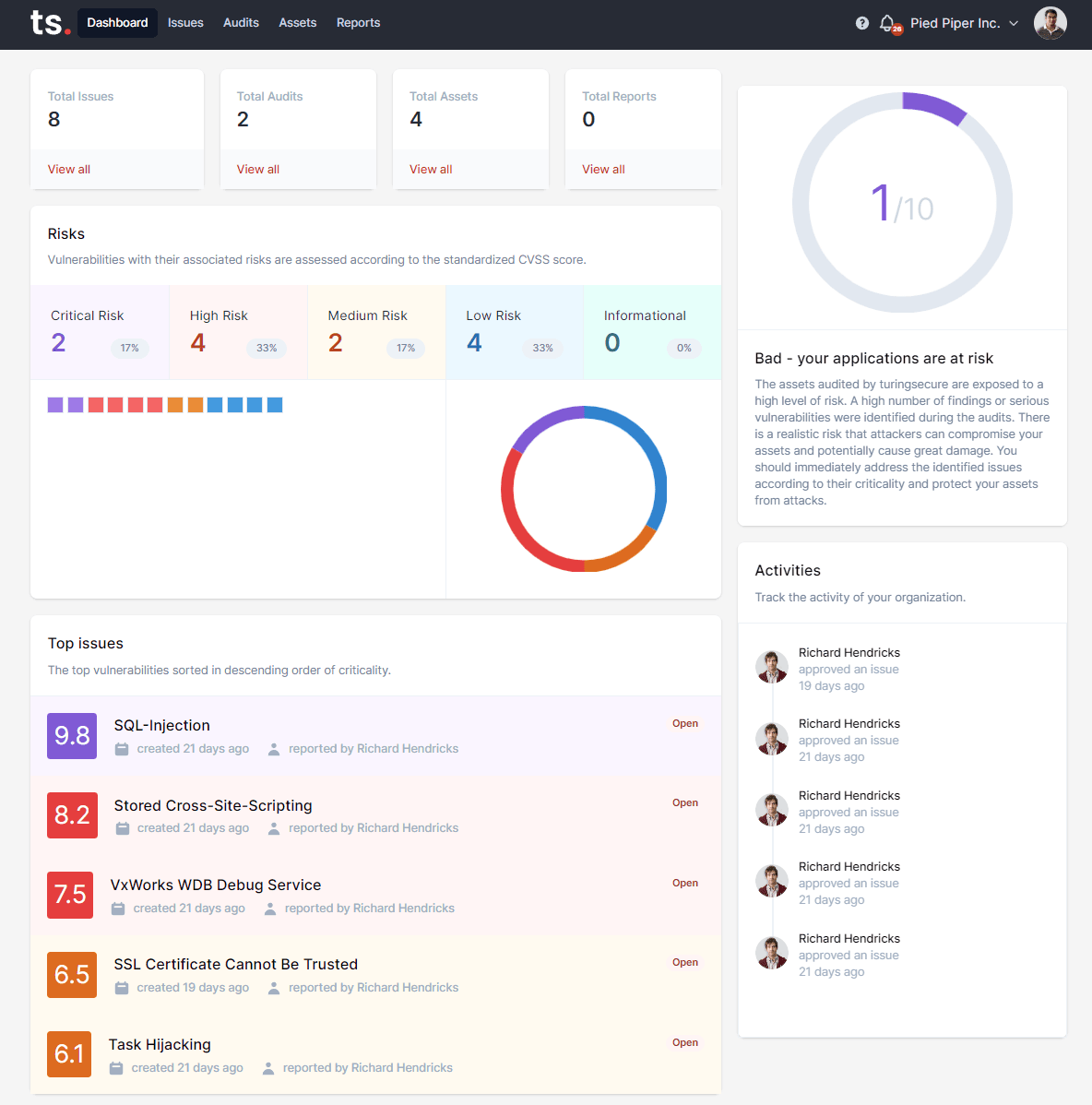
Penetration Testing as a Service (PTaaS)
Penetration Tests on the turingsecure Platform
We offer comprehensive vulnerability management for customers, partners, penetration testers, and IT security consultants. Use our software products to also get the best technologies and reporting tools on the market.
Comprehensive Solutions for Your Application Security
With our comprehensive and intuitive platform, you can now map the entire security process of your applications.
- Continuous Application Security Testing
Continuous Security Application Testing (CAST) ensures that applications are examined for vulnerabilities in a regulated cycle. Our methodology allows for direct integration into the agile development process, thus enabling a high level of continuous security.
- On-Demand Penetration Testing
Penetration testing of applications is scaled as needed to meet more complex requirements. For a demanding application, a quick and manual penetration test can be conducted to identify vulnerabilities in your application's business logic.
- Vulnerability Management & Reporting
turingsecure can classify, prioritize, and identify all vulnerabilities related to application security. All findings are graphically processed for a better insight. A management summary, vulnerability details, and remediation steps can be exported in PDF and machine format.
Linkable on your website
Certification with Seal
We have developed an effective and comprehensive format for verifiable security that can be directly integrated into your website. This certificate demonstrates to third parties such as customers or insurance companies a high level of security, data protection, and an awareness of IT security.
The certificates we issue demonstrate a high level of IT security at a given point in time according to a standard or individual test modules. Depending on the assessment, different test guidelines are selected and evaluated.

Our E-Book
eBook: Finding the Right Pentest Provider
Finding the right provider for pentests can be a problematic process, especially for those who are not familiar with IT security. What do I need? How do I know who can demonstrate sufficient technical expertise? How do I identify unqualified pentest providers? How do I recognize good reputation and competence? What should the documentation look like?
In this eBook, we provide you with 6 questions you should ask potential service providers for your next penetration test. You will know what to look for when selecting a provider, how to compare the various offers, and ultimately make the best choice for your specific requirements.

Current Information
Recent Blog Articles
Our employees regularly publish articles on the subject of IT security
Contact
Curious? Convinced? Interested?
Schedule a no-obligation initial consultation with one of our sales representatives. Use the following link to select an appointment: