OWASP Top 10 Mapping: From 2021 to 2025
The OWASP Top 10:2025 introduces two new categories, one rename, and a quiet goodbye to SSRF. What that means for pentest scopes and finding templates.

Why This Mapping Matters Now
The OWASP Top 10:2025 is the first major revision in four years. If your pentest reports are keyed to the 2021 categories, if your finding templates are named after them, or if your compliance evidence references them, you need a clean translation. Two categories are new, two were renamed, one has disappeared as a standalone entry, and the ordering has shifted noticeably. That looks cosmetic at first glance — until you look at test plans, acceptance criteria, or ISMS references.
This article is a companion piece to our overview of the 2021 OWASP Top 10 and deliberately focuses on the deltas.
The OWASP Top 10:2025 at a Glance
A01:2025 Broken Access Control
A02:2025 Security Misconfiguration
A03:2025 Software Supply Chain Failures
A04:2025 Cryptographic Failures
A05:2025 Injection
A06:2025 Insecure Design
A07:2025 Authentication Failures
A08:2025 Software or Data Integrity Failures
A09:2025 Security Logging and Alerting Failures
A10:2025 Mishandling of Exceptional Conditions
Broken Access Control holds onto the top spot without challenge. Security Misconfiguration jumps from A05 to A02, which matches what pentesters have been seeing in the field for years: misconfigured cloud services, over-permissive IAM policies, and untouched default settings are among the most common working entry vectors.
Mapping Table 2021 to 2025
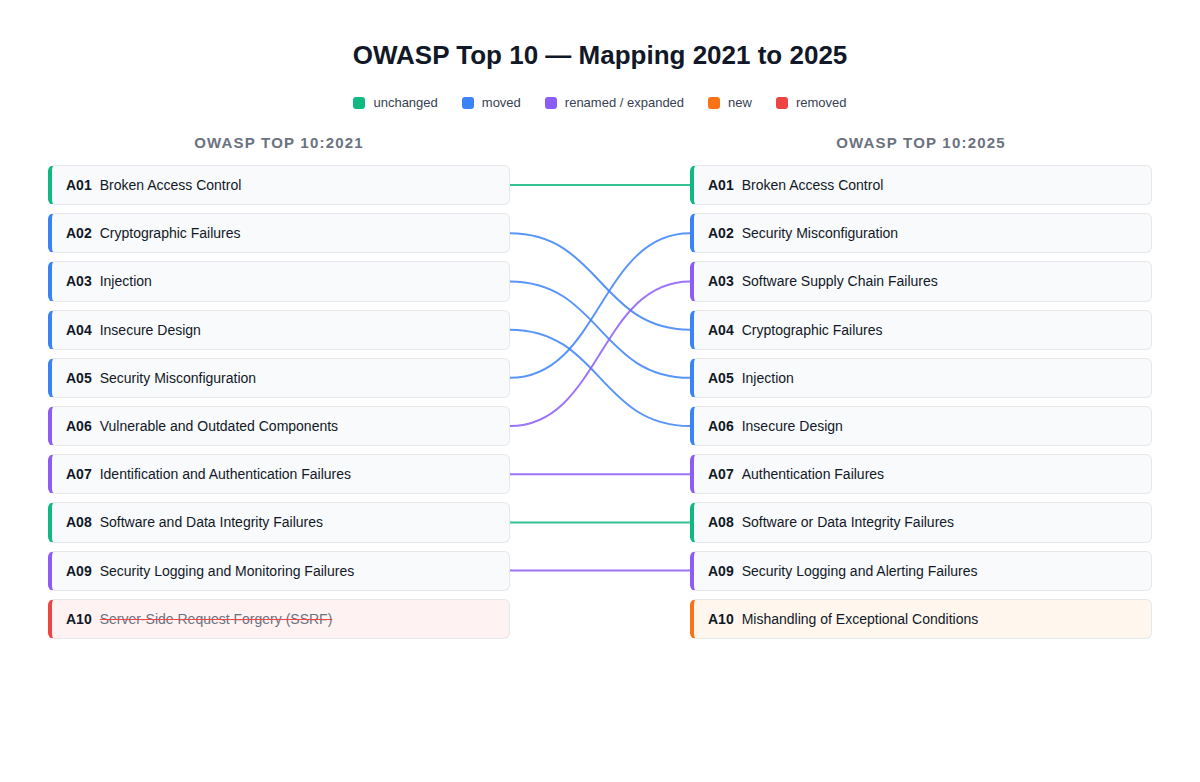
| 2021 | 2025 | Change |
|---|---|---|
| A01 Broken Access Control | A01 Broken Access Control | unchanged |
| A02 Cryptographic Failures | A04 Cryptographic Failures | rank −2 |
| A03 Injection | A05 Injection | rank −2 |
| A04 Insecure Design | A06 Insecure Design | rank −2 |
| A05 Security Misconfiguration | A02 Security Misconfiguration | rank +3 |
| A06 Vulnerable and Outdated Components | A03 Software Supply Chain Failures | renamed, expanded, rank +3 |
| A07 Identification and Authentication Failures | A07 Authentication Failures | renamed |
| A08 Software and Data Integrity Failures | A08 Software or Data Integrity Failures | wording refinement |
| A09 Security Logging and Monitoring Failures | A09 Security Logging and Alerting Failures | renamed |
| A10 Server-Side Request Forgery (SSRF) | — | removed as standalone category |
| — | A10 Mishandling of Exceptional Conditions | new |
Software Supply Chain Failures (New on A03)
The 2021 category was called "Vulnerable and Outdated Components" and was essentially an SCA checklist: find known-vulnerable libraries, patch them, done. The 2025 version is substantially broader. According to OWASP, it now covers "breakdowns or other compromises in the process of building, distributing, or updating software" — the entire delivery chain, including build pipelines, signature verification, registry trust, and unmaintained components.
The mapped CWEs reflect that shift. Alongside the familiar CWE-1035 (Using Components with Known Vulnerabilities), the category now includes CWE-1104 (Unmaintained Third Party Components), CWE-1329 (Reliance on Component That is Not Updateable), and CWE-1357 (Reliance on Insufficiently Trustworthy Component).
For pentests this means concretely: scanning package-lock.json for CVEs no longer covers the category. It now also raises questions like: Who can write into the build pipeline? Are internal artifacts signed and verified at deployment time? Does the codebase depend on packages whose maintainers have been inactive for years? For a deeper dive, the CNCF Software Supply Chain Security Paper is a solid starting point.
Mishandling of Exceptional Conditions (New on A10)
Behind the awkward name sits an old acquaintance: poor error handling. The category bundles 24 CWEs that revolve around how an application responds to unexpected states — from verbose stack traces in HTTP responses (CWE-209) to NULL pointer dereferences (CWE-476), fail-open behavior on authentication checks (CWE-636), race conditions, and resource leaks under load.
This is not a new class of vulnerability, but in 2021 it had no dedicated home. Many findings that pentesters used to file under "Information Disclosure" or "Insecure Design" now fit cleanly here. If you maintain a finding template, create a dedicated bucket for this category — otherwise you will end up with ambiguous mappings.
SSRF Is Not Gone, Just No Longer Standalone
Server-Side Request Forgery was added as A10 in 2021 with a brief nod to survey data. In the 2025 version it no longer appears as a standalone category. SSRF has not disappeared from the landscape — it is typically classified under Broken Access Control (missing validation of internal endpoints) or Insecure Design (no architectural separation between internal and external requests).
For test plans this means: SSRF obviously stays part of every web application pentest — only the reporting category changes. Cloud pentest practitioners will continue to see SSRF in the context of IMDS access (EC2, GCE) and metadata service escalation — and that fits Broken Access Control more cleanly anyway.
Quiet but Meaningful Renames
Two renames look like wording polish but are substantively relevant:
A07: Authentication Failures (formerly "Identification and Authentication Failures") sharpens the focus on authentication itself. In its 2025 guidance OWASP explicitly references NIST SP 800-63B and calls out newer attack patterns such as hybrid password spraying. If MFA bypass tests, session fixation, or credential stuffing are already in your pentest scope, the scope largely carries over — but the expectation now is that tests run against 800-63B-compliant implementations.
A09: Security Logging and Alerting Failures (formerly "Logging and Monitoring") shifts emphasis. Logs alone no longer suffice. A category-aligned implementation now requires active alerting backed by working playbooks. For pentests executed against a SOC or blue team, the question becomes whether generated events actually translate into actionable alerts — or vanish into noise.
Implications for Pentest Scoping and Finding Templates
Teams that structure pentests by OWASP category should adjust three things:
- Rename the finding template, not just the category ID. A finding filed in 2023 under "A06 Vulnerable Components" belongs in the broader 2025 class "Software Supply Chain Failures" — with the consequence that pipeline and artifact security tests need to come along into scope.
- Reclassify SSRF findings. The cleanest placement is under Broken Access Control when internal resources were reachable without an authorization check, or under Insecure Design when the architecture never enforced the separation in the first place.
- Add a dedicated bucket for Mishandling of Exceptional Conditions. Stack traces in error pages, uncaught exceptions, race conditions, and fail-open logic finally get a proper home and stop bleeding into categories that are too broad.
For buyers this flips around: before the next pentest it is worth a glance at the requirements document. If it still references "A10 SSRF," that is not wrong — but it is no longer aligned with the current reference.
How This Relates to the Other OWASP Lists
The Top 10 is not the only OWASP list relevant to pentests. For mobile applications the OWASP Mobile Top 10 remains the right framework; for container environments it is the OWASP Kubernetes Top 10. For the broader OWASP ecosystem (ASVS, Testing Guide, Cheat Sheets) our overview of the OWASP framework for web applications is a good entry point.
Conclusion
The OWASP Top 10:2025 is less of a revolution than the 2021 edition, but it is more precise in the places that matter: supply chain risk gets a dedicated and cleanly scoped category, exceptional-condition handling finally has a home, and renaming "Monitoring" to "Alerting" captures what audits have been demanding anyway. For pentest teams this mainly means housekeeping in templates and scoping documents — and a good excuse to walk through the last two years of findings and tighten up the mapping where it has drifted.