Classifying IT Vulnerabilities with CVSS
CVSS is an open industry standard for assessing the severity of software vulnerabilities. This assessment is a fundamental component of any penetration test.

What Is the Common Vulnerability Scoring System?
CVSS is an open industry standard for assessing the severity of software vulnerabilities. This standard enables a consistent evaluation of the vulnerability of computer systems and the severity of security flaws. As a result, vulnerabilities and their impact on the overall system landscape can be better understood and communicated in a uniform manner.
Vulnerability Assessment in Penetration Testing
A vulnerability assessment is a fundamental component of any penetration test. Without insight into potential threats, it is difficult to determine where security investments and resources should be focused. A vulnerability assessment identifies, quantifies, and prioritizes the weaknesses in a system. It captures recognized threats as well as the likelihood that they will lead to a compromise or data loss. Through this combined assessment, a comprehensive understanding of existing vulnerabilities, threats, and the probability of their exploitation is established.
History of CVSS
Research by the National Infrastructure Advisory Council (NIAC) in 2003 and 2004 led to the introduction of CVSS Version 1 in February 2005. The goal was to provide open and universally standardized severity ratings for software vulnerabilities. However, this initial draft had not undergone peer review or scrutiny by other organizations. In April 2005, the NIAC selected the Forum of Incident Response and Security Teams (FIRST) as the custodian of CVSS for future development.
Feedback from vendors using CVSSv1 in production revealed significant issues with the original design. Work on CVSS Version 2 (CVSSv2) began in April 2005; the final specification was published in June 2007.
Further feedback led to work on CVSS Version 3 beginning in 2012, which concluded with the release of CVSSv3 in June 2015.
The Benefits of CVSS in Penetration Testing
CVSS Measures Severity, Not Individual Risk
The CVSS specification document was updated to clarify that CVSS measures the severity of a vulnerability and should not be used as the sole basis for risk assessment.
In practice, the CVSS Base Score was sometimes used in situations where a comprehensive risk assessment would have been more appropriate. The CVSS v3.1 specification document now explicitly states that the CVSS Base Score represents only the intrinsic characteristics of a vulnerability that remain constant over time and across user environments. The CVSS Base Score should be supplemented by a contextual analysis of the specific environment, taking temporal and environmental CVSS metrics into account. Ideally, a comprehensive risk assessment system should be employed that goes beyond the CVSS Base Score alone. Such systems typically also consider factors outside the scope of CVSS, such as exposure and the concrete threat landscape.
Communicating Vulnerabilities Consistently Through Interoperability
A unified standard promotes cross-organizational collaboration, as all parties share the same understanding of a vulnerability's severity. Further discussions and assessments can take place on the basis of this framework, which increases efficiency, avoids inconsistencies, and provides a clear process guide for the often challenging communication about IT vulnerabilities.
Which Metrics Are Used and How Scores Are Calculated
Base, Temporal, and Environmental Metric Scores
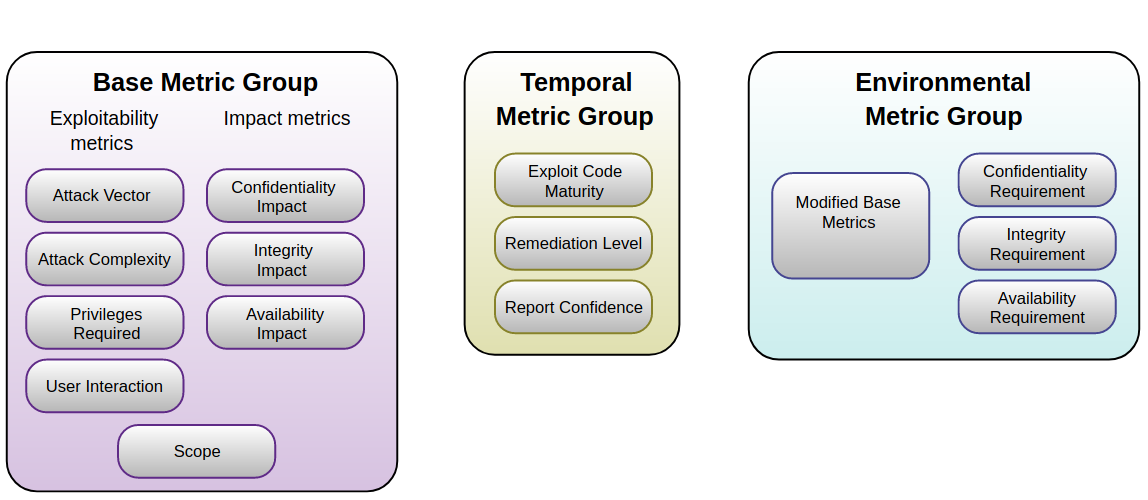
The Base Metric Group represents the intrinsic characteristics of a vulnerability that remain constant over time and across different user environments. It consists of two subgroups: the Exploitability Metrics and the Impact Metrics.
The Exploitability Metrics describe how easily and by what technical means a vulnerability can be exploited. They represent the properties of the Vulnerable Component. The Impact Metrics capture the direct consequences of a successful exploitation for the affected component.
The Vulnerable Component is typically a software application or module. The ability to also measure the impact on components other than the directly vulnerable one was a key feature introduced with CVSS v3.0. This property is captured by the Scope metric.
The Temporal Metric Group represents characteristics of a vulnerability that may change over time but do not vary across different user environments. For example, the availability of an easy-to-use exploit kit would increase the CVSS score, while the release of an official patch would lower it.
The Environmental Metric Group captures characteristics of a vulnerability that are relevant and unique to a specific user's environment. These include, for example, existing security controls that can mitigate some or all consequences of a successful attack, as well as the relative importance of a vulnerable system within the technological infrastructure.
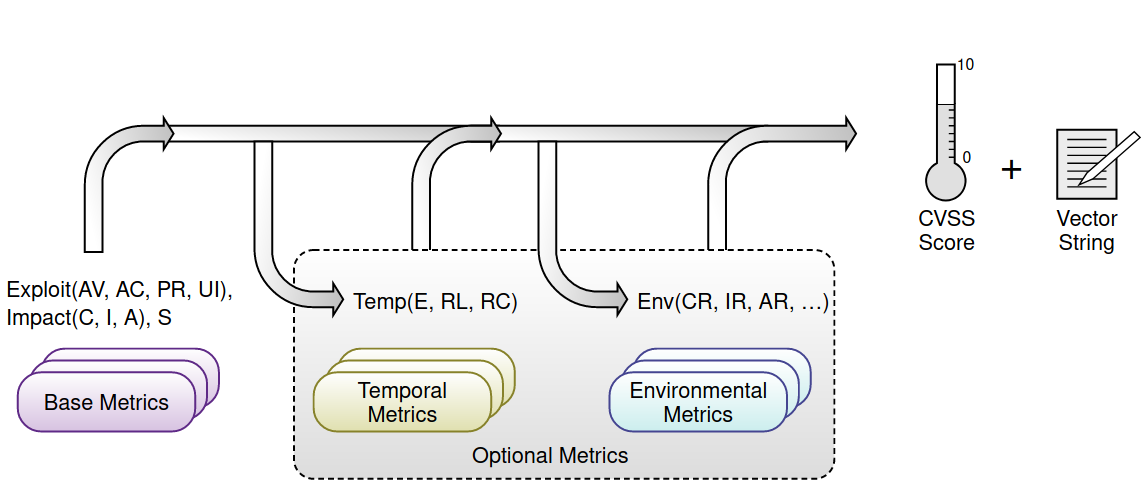
The Base equation is composed of two sub-equations: the Exploitability Sub-Score and the Impact Sub-Score. The Exploitability Sub-Score is derived from the Base Exploitability Metrics, while the Impact Sub-Score is derived from the Base Impact Metrics.
The Base Score can then be refined through temporal and environmental metrics to more accurately reflect the relative severity that a vulnerability poses in a specific user environment at a given point in time. Evaluating these additional metrics is not mandatory but is recommended for more precise results.
Typically, the Base and Temporal Metrics are provided by security analysts, security product vendors, or application vendors, as they possess the most detailed information about a vulnerability's characteristics. The Environmental Metrics, on the other hand, are set by end-user organizations, as they are best positioned to assess the potential impact of a vulnerability within their own IT environment.
CVSS Score Ratings
For each vulnerability, CVSS assigns a severity score ranging from 0.0 (lowest severity) to 10.0 (highest severity), enabling you to prioritize remediation efforts more effectively.
| Severity | Base Score Range |
|---|---|
| None | 0.0 |
| Low | 0.1 - 3.9 |
| Medium | 4.0 - 6.9 |
| High | 7.0 - 8.9 |
| Critical | 9.0 - 10.0 |
Easy Calculation with the CVSS Calculator
We recommend the official CVSS calculator from FIRST.org, which allows penetration testers, clients, and developers to easily perform or adjust CVSS calculations. Advanced users can generate a score in just a few clicks. Additionally, the calculator offers an intuitive wizard with helpful guidance, enabling beginners to correctly calculate a CVSS score as well.
CVSS Calculator from FIRST.org
Conclusion
CVSS scores are instrumental in taking appropriate action after a penetration test and in developing secure software products, infrastructures, and mobile applications. Every professional final report should include an assessment based on this framework, so that clients can understand the severity of findings and follow-up discussions can take place on a consistent CVSS basis.