Differences Between CVSS V3.1 and V4.0
On November 1, 2023, the Common Vulnerability Scoring System Version 4 (CVSS v4) was officially introduced as an update for version v3.1.
On November 1, 2023, the Common Vulnerability Scoring System Version 4 (CVSS v4) was officially released into general availability, following a period of public preview and feedback. Coordinated by the Forum of Incident Response and Security Teams (FIRST), it marks a significant update to the CVSS standard, which was last revised over eight years ago with the release of CVSS v3.0 in June 2015. The goal of this latest version is to provide improved accuracy in vulnerability assessment.
This new version includes several refinements, such as a more detailed breakdown of base metrics for a more nuanced understanding and assessment of vulnerabilities. CVSS v4 also introduces new nomenclature for combinations of base, threat, and environmental metrics, as well as new base metric values for user interaction categorized as either passive or active. For a more in-depth look at these changes, please refer to our detailed blog article.
The success of CVSS v4 depends on widespread adoption by the cybersecurity community, the clarity and usability of its refined metrics, and accurate vulnerability assessment. Integration with existing systems, vendor support, and active community and regulatory involvement are all critical factors. Its real-world effectiveness, combined with a feedback mechanism for continuous improvement and timely updates in response to emerging threats, will determine its long-term impact on cybersecurity practices.
What's New in CVSS v4.0?
Terminology
The CVSS framework has always consisted of three metric groups: Base, Temporal, and Environmental. In practice, however, the CVSS base score became synonymous with the overall CVSS score. Since the CVSS score encompasses more than just the base score, CVSS v4 introduced the following new nomenclature:
- CVSS-B: Base Metrics
- CVSS-BE: Base and Environmental Metrics
- CVSS-BT: Base and Threat Metrics
- CVSS-BTE: Base, Threat, and Environmental Metrics
New Base Metric: Attack Requirement (AT)
The new Attack Requirement (AT) metric provides a more detailed view of Attack Complexity (AC). It captures the prerequisites and execution conditions of the vulnerable system that enable the attack.
- Attack Complexity -- Reflects the effort required to develop exploits that bypass or overcome defensive or security-enhancing technologies.
- Attack Requirements -- Reflects the prerequisites of the vulnerable component that enable the attack.
Supplemental Metric Group
CVSS v4.0 introduces a new optional metric group called the "Supplemental Metric Group." It provides metrics that describe and measure additional extrinsic characteristics of a vulnerability. The goal is to offer contextual information that users can leverage for further risk analysis. Importantly, supplemental metrics are optional and do not affect calculated CVSS scores. They help you better understand extrinsic aspects of vulnerabilities, such as:
- Safety: Does exploiting this vulnerability impact the physical safety of people?
- Automatable: Can attackers automate exploitation of this vulnerability?
- Recovery: Can affected systems and components recover on their own after an attack?
- Value Density: What resources does the attacker gain control of with a single exploit?
- Provider Urgency: How urgently does the vendor rate this vulnerability?
CVSS v3.1 vs CVSS v4.0
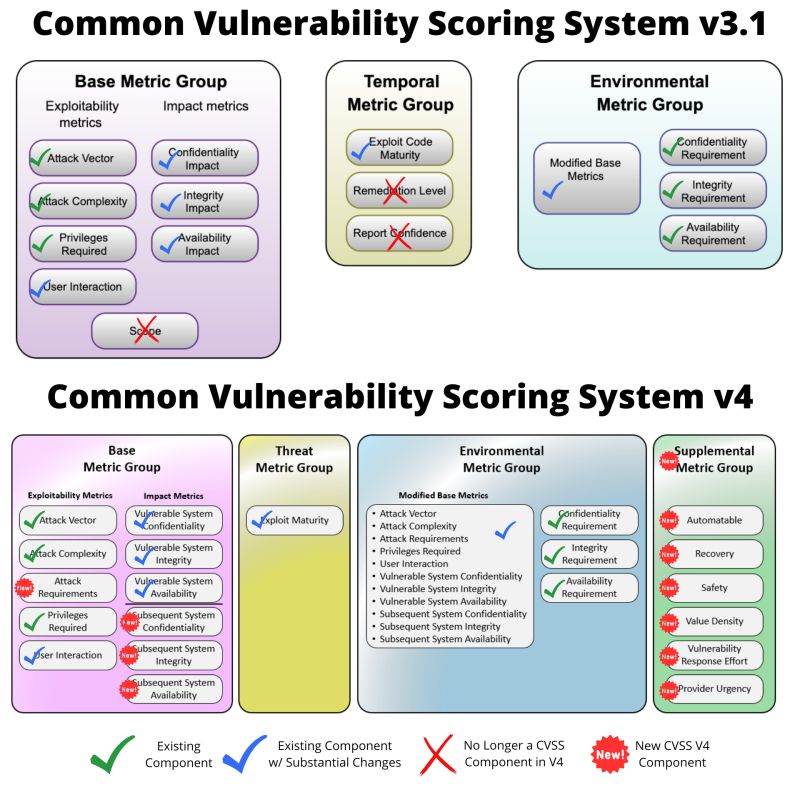
The figure above provides an overview of the changes between CVSS v3.1 and CVSS v4.0.
What Has Been Updated in CVSS v4.0?
CVSS v4.0 provides improved guidelines for CVSS analysts to produce more consistent scores, along with guidance for assessing vulnerabilities in software libraries. The new version supports multiple CVSS scores for the same vulnerability when it affects different platforms, products, and operating systems. It also includes guidelines for extending the CVSS framework to other industries such as data protection, privacy, and the automotive sector.
Renaming and Simplified Threat Metrics
CVSS v4.0 renamed the "Temporal Metric" from CVSS v3.1 to "Threat Metrics." The "Remediation Level (RL)" and "Report Confidence (RC)" metrics were retired. Additionally, "Exploit Code Maturity (E)" was renamed to "Exploit Maturity (E)." The values "High (H)" and "Functional (F)" from CVSS v3.1 were merged into a single value of "Attacked (A)" in CVSS v4.0.
Updated Base Metric: User Interaction (UI)
This metric captures whether a user other than the attacker must participate in the successful compromise of the vulnerable component. CVSS v3.1 offered only None (N) or Required (R) for user interaction. CVSS v4.0 provides greater granularity with two new values: Passive (P) or Active (A).
Deprecated Base Metric: Scope (S)
The CVSS v3.1 base metric Scope (S) was retired in CVSS v4.0 due to a lack of clarity around its usage. This had led to inconsistent vulnerability assessments across different product vendors. The scope metric was replaced by two separate impact metrics:
- Vulnerable System Impact -- Confidentiality (VC), Integrity (VI), Availability (VA)
- Subsequent System(s) Impact -- Confidentiality (SC), Integrity (SI), Availability (SA)
Assessment of Vulnerabilities in Software Libraries
New guidelines explain how to assess the impact of a vulnerability in a library.
Guidance on Environmental Security Requirements Metrics
The Environmental Metric Group includes three security requirement metrics: Confidentiality Requirement, Integrity Requirement, and Availability Requirement for the vulnerable system.