Maturity Analysis of the IT Security Organization
Every IT security organization should evaluate at which stage the measures already taken are in order to avoid redundant security analyses.

Every IT security organization should evaluate the current state of its existing measures to avoid redundant security analyses. To this end, it is important to define the company's current maturity level, since the various security assessments -- such as pentesting -- build on each other. In addition, legal and regulatory requirements often apply depending on the relevant industry, markets, or countries. It would not make sense to conduct a complex attack simulation if no simple vulnerability scan or penetration test has been performed beforehand, because the chance of success would be nearly 100%, rendering the findings meaningless.
After defining the different maturity levels, this article answers the question:
When does which IT security service make sense?
Technical and Organizational Measures
Technical and organizational measures (TOM) are the measures prescribed by Art. 32 of the General Data Protection Regulation (GDPR) to ensure the security of the processing of personal data. All described measures fall under the principle of proportionality, meaning that service providers do not necessarily need to implement the same protective measures as the client. Every IT manager should thoroughly address these measures in order to develop a data-protection-compliant, company-wide concept. For more information about TOMs, please visit IBM.
Technical Measures
Technical measures directly affect data processing. They encompass all measures that ensure IT security -- from the systems in use to the physical security of the building.
Examples of this subcategory include:
- Encryption of data media and data transmissions
- Automatic backups
- Availability control
- Pseudonymization
- Restorability
- Input control (revision security and user identification)
- Access control
- Transfer control
Organizational Measures
Organizational measures define the framework conditions for technical processing. They represent all non-technical measures.
Examples of this subcategory include:
- Emergency management
- Entry control
- Order control
- Employee training in data protection
- Separation control
- Confidentiality obligations for employees
- Data protection management
- Dual-control principle
IT Vulnerability Analysis
This type of security analysis is the simplest security assessment. It evaluates how secure the internal IT infrastructure is against external or internal attackers. It provides a solid overview of the organization's attack surface, and the resulting findings form the basis for more advanced assessments such as penetration testing.
The analysis identifies IT vulnerabilities that are already known or caused by outdated software. In many cases, the associated risk can be mitigated through active and consistent patch management. Complex vulnerabilities cannot be uncovered with a vulnerability check alone, as no in-depth analysis is performed.
Penetration Test
In a pentest, manual evaluation takes center stage, since automated security scans cannot replicate complex attack chaining. Pentesting is therefore one of the more demanding IT security audits, as multiple low-criticality vulnerabilities can be combined into a severe security flaw. Process-related weaknesses in the business logic of web or API components are also frequently discovered, making an independent review of the IT infrastructure, web applications, and mobile apps essential. A penetration test always includes details about each vulnerability along with comprehensive remediation steps for IT stakeholders and developers.
A thorough examination of both software and hardware is essential for a high level of IT security!
Attack Simulation
Attack simulations, often called Red Teaming, go far beyond pure infrastructure and application security. They emulate a malicious actor who actively attacks and attempts to evade detection -- similar to an Advanced Persistent Threat (APT). Spearphishing attacks also fall into this category, as they test the responsiveness of internal IT processes. Phishing attacks are a form of digital social engineering and often serve as the starting point for lateral movement.
The goal is always to demonstrate a successful data exfiltration and an immediate threat that mirrors a real-world incident. An attack simulation therefore tests IT processes and employees by actively challenging them through a malicious actor.
The Maturity Model of IT Security
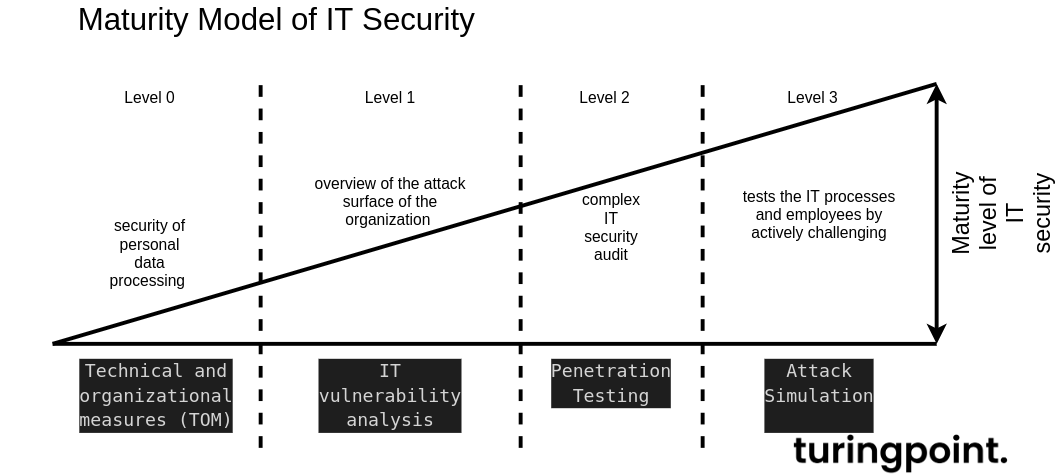
The maturity of a company or process is measured against a development path divided into levels. A specific level is reached depending on the organization's capability. IT security maturity values are defined by specific criteria in relation to maximum achievable states. The optimum would be reached when an organization can withstand a continuous attack simulation.
Conclusion
A comprehensive maturity model should be developed to assess where processes and the organization need to evolve and whether security standards such as IT-Grundschutz, BSI 100-x, and ISO 2700x are relevant. If no measures have been taken yet, the first step should be establishing technical and organizational measures. Only then should a penetration test be conducted -- followed by an attack simulation once the hardening measures have been implemented. All described security assessments are part of an effective information security management with IT-Grundschutz and ISO 27001.