Man-in-the-Browser Attacks
The man-in-the-browser attack is a form of man-in-the-middle attack in which an attacker takes control of the browser.

A man-in-the-browser attack is a variant of the man-in-the-middle attack in which an attacker takes control of the browser and positions themselves between the graphical content displayed to the user and the server. From this position, the attacker can intercept and manipulate requests at will. This type of attack is most commonly used for financial fraud, typically by tampering with online banking services. The malware involved is usually a Trojan. For everyday users, the attack is extremely difficult to detect because all expected controls and security mechanisms continue to function normally, even when SSL is in use.
How Does a Man-in-the-Browser Attack Work?
A man-in-the-browser attack typically relies on Trojan malware that runs within a specific browser process -- in most modern web browsers, this corresponds to an individual tab. Once the victim begins browsing, the malware attaches itself to these tabs. The three most common attack vectors are:
Compromised Browser Extensions
Browser extensions are add-on modules that enhance a browser's functionality and allow users to customize their experience. They can read cookies and other data, manipulate DOM elements, and issue POST and GET requests. Because most modern extensions consist entirely of source code, they may also contain vulnerabilities that an attacker can exploit to inject malicious code.
API Hooking
Browsers depend on operating system APIs and DLLs to function properly. A Windows-based web browser, for example, may use the wininet DLL to send and receive HTTP requests. Malware can intercept and alter the API call flow, inserting itself as a man-in-the-middle between the API and the requesting process. This gives the attacker extensive control over the process's behavior.
Malicious Content Scripts
Content scripts are script files that execute within the context of a web page in the user's browser. They can read and manipulate web pages through the Document Object Model (DOM). Malicious content scripts can be injected into web pages in two ways: by compromising the web page directly on the hosting server, or by using MITM techniques to tamper with the HTTP response sent to a specific client.
Man-in-the-Browser Attack Example
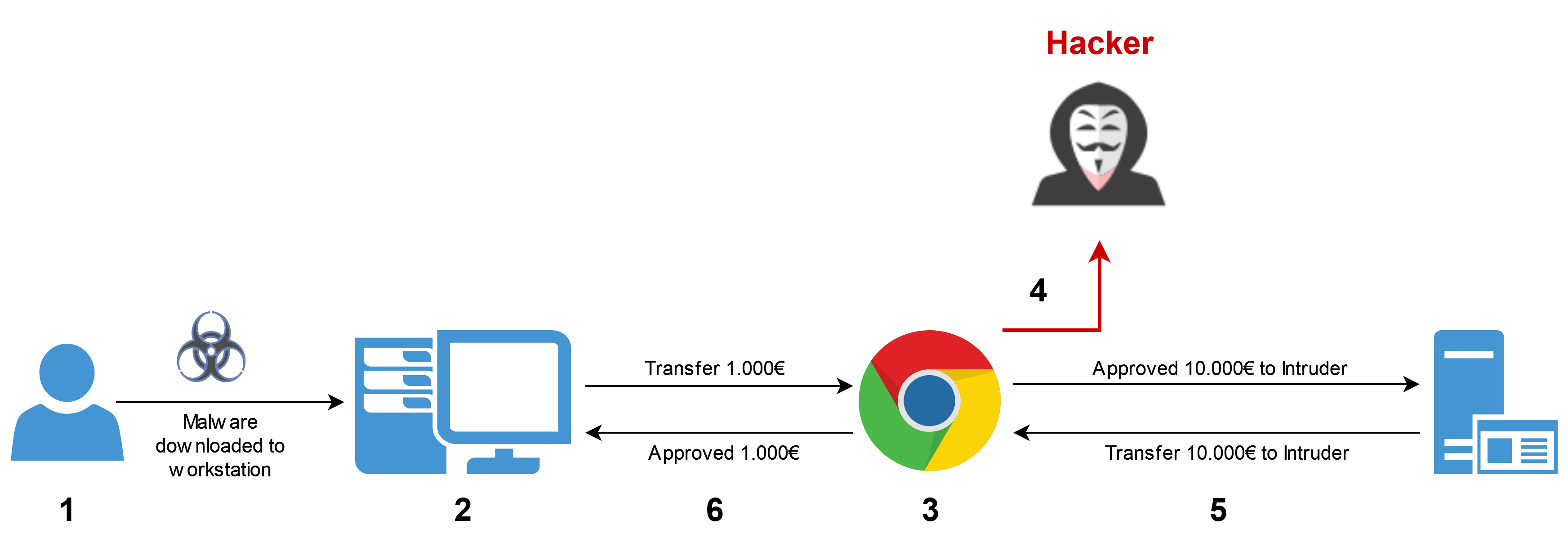
- The victim's computer is infected with a MITB Trojan through a social engineering attack
- The Trojan embeds itself in the computer's web browser
- The victim logs into their online banking site to initiate a transfer
- The malware intercepts and modifies the transaction
- The funds and confirmation are redirected to the attacker
- The malware displays a convincing confirmation page to the victim, indicating that the requested transfer was successful
Reducing the Risk of Man-in-the-Browser Attacks
There are several ways to mitigate the risk of a man-in-the-browser attack. One approach is to restrict user privileges, making it harder for an attacker to access administrator-level processes. However, this typically comes at the cost of usability.
User awareness is equally important. Employees should be trained to identify suspicious browser extensions. Since there are usually no visible signs that a browser has been compromised, users should be encouraged to close browser sessions regularly when they are no longer needed. In addition, training to recognize and resist social engineering attacks is highly recommended.
Another effective countermeasure is keeping antivirus software up to date. Because many MITB malware variants contain static code files, they can be reliably detected and removed by antivirus solutions. Additionally, applications and software should only be downloaded from trusted sources.
How to Detect Man-in-the-Browser Attacks
One of the biggest challenges with MITB attacks is detection. Legitimate user traffic masks the attacker's activity, no new processes are spawned, and malicious logins are nearly indistinguishable from normal ones.
Nevertheless, there are subtle indicators that may point to a MITB attack:
- Additional or missing elements appear on the website
- You receive a login notification from an unrecognized device
- You are unexpectedly logged out of your account
- Your antivirus software detects malware on the computer
Conclusion
Man-in-the-browser attacks rank among the most effective methods for committing online financial fraud. The good news is that while these attacks are hard to detect, they are comparatively easy to prevent. A MITB attack cannot succeed without first installing a Trojan on the target system. By deploying robust security software, maintaining strict user account management, and providing targeted employee training, organizations can significantly reduce the risk of their workforce falling victim to a MITB attack.