Email Encryption with PGP
The purpose behind using PGP is that sent messages cannot be intercepted and read by anyone during transmission because of the encryption.

Introduction
PGP stands for Pretty Good Privacy, but it delivers far more than the name suggests. In fact, PGP is the most widely used email encryption system available today. It ensures that sent messages cannot be intercepted or read by anyone during transmission. Over its many years of use, PGP has been thoroughly tested, and the few known vulnerabilities have been addressed.
What Is PGP?
PGP is a cryptographic method that enables encrypted communication. When a message is sent using PGP, it is first converted into unreadable ciphertext. Only the recipient holds the key to convert the text back into a readable message on their device.
PGP also authenticates the sender's identity and ensures the message has not been tampered with during transmission.
Before email encryption existed, an attacker could theoretically read all messages. PGP was developed in the 1990s to enable the private exchange of emails and other message types. Today, PGP is standardized as OpenPGP and has become a cornerstone of email security. This is one of the key reasons it is widely used to protect both individuals and organizations.
How Does PGP Work?
PGP combines two encryption methods: symmetric encryption (a one-time session key that encrypts and decrypts the message) and public-key encryption (recipient-specific keys that encrypt and decrypt the session key). In this article, we focus on the fundamental concepts.
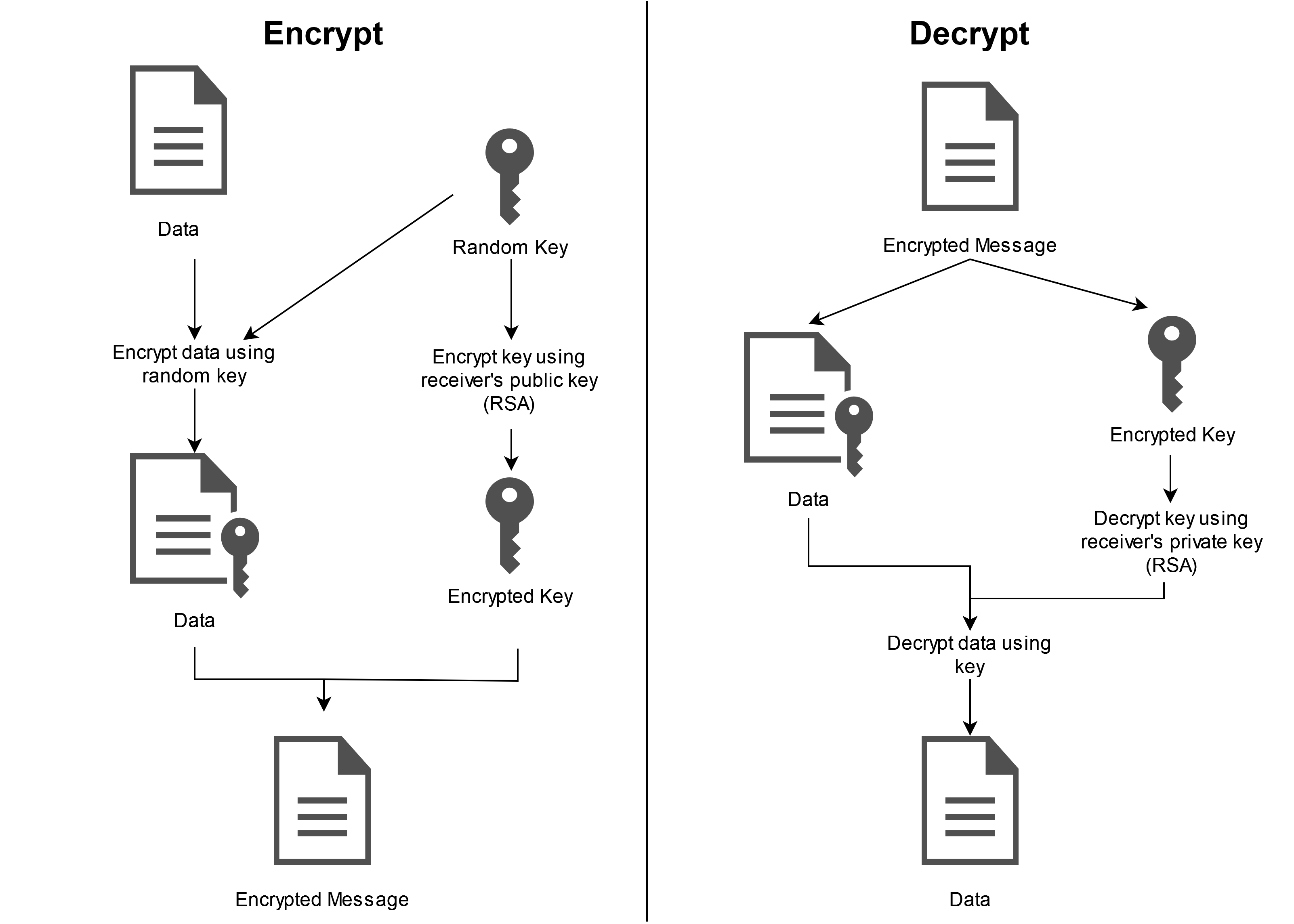
First, PGP generates a random session key. This key is a very large number used to encrypt and decrypt the message contents. Only someone who knows the session key can read the message. Since the key is extremely large, guessing it is virtually impossible. Each session key is used only once and never reused for other messages.
The session key is then encrypted with the recipient's public key. The public key is unique to each person and can be freely shared. Since it does not change, it functions much like an email address: it is tied to one person, and anyone can use it to send that person an encrypted message.
This additional encryption step is necessary because public-key cryptography is much slower than symmetric cryptography, especially for large messages. Encrypting and decrypting large emails or files directly with a public key would require significant time and computing power. Instead, public-key cryptography is used solely to encrypt the session key.
Using symmetric cryptography alone would be impractical because the session key must somehow be securely shared with the recipient. Transmitting the session key in plaintext would be insecure, as anyone who intercepts it could decrypt the entire message.
Sharing the session key through a separate encrypted channel or in person would be impractical for online communication. PGP therefore combines the efficiency of symmetric encryption with the security of public-key encryption.
Signature
The public key serves an additional function: signing and verifying emails. If an email recipient is uncertain about the sender's identity, they can use PGP's digital signature feature to verify it.
When signing, a hash algorithm generates a hash value of the message. This hash is then signed with the sender's private key, and the resulting signature is appended to the message.
Verification uses the sender's public key to decrypt the encrypted hash value and compare it with the hash of the received message. If the values do not match, the recipient knows the message was altered during transmission. This reveals whether the sender is who they claim to be, whether a forged digital signature was used, or whether the email has been tampered with.
Web of Trust
Unlike S/MIME, PGP does not rely on a central certification authority to confirm a key's trustworthiness. Instead, PGP is built on mutual trust between users. Each PGP user authenticates the public keys of trusted contacts by signing them with their own private key. This confirms that a given public key genuinely belongs to the person it claims to represent.
Through this mutual authentication, a decentralized network of trust emerges, known as the "Web of Trust".
How Secure Is PGP?
PGP is generally considered secure for encrypting email content. However, this does not extend to email metadata such as sender, recipient, subject, date, or IP address.
The primary challenge with PGP lies on the user side: you must manage your own keys and build a "Web of Trust" independently. PGP's security depends on keeping the private key and its associated password confidential. The encryption remains secure only as long as this information stays secret and inaccessible to others.
Additionally, it is advisable to use the longest key possible to make cracking the encryption as time-consuming as possible.
Disadvantages of PGP
The biggest disadvantage of PGP is its limited usability, which means that using PGP can involve considerable additional effort. Moreover, users should understand how PGP works to avoid introducing vulnerabilities through incorrect use.
Both sender and recipient must use compatible versions of PGP. Otherwise, the recipient cannot decrypt the content and the message remains unreadable.
Conclusion
Encrypting emails with PGP is generally recommended, as the method continues to be considered secure. Keep in mind, however, that both communication partners must use PGP in order to read encrypted messages.