What Is Open Source Intelligence?
Open Source Intelligence, or OSINT for short, refers to the collection of information from public sources for use in the context of intelligence.
Open Source Intelligence, or OSINT for short, refers to the systematic collection and analysis of information from publicly available sources. The term originated in the military domain, where it described the strategic gathering of open-source information to produce actionable intelligence. Today, OSINT extends well beyond cybersecurity and is equally relevant to corporate intelligence, business analysis, and national security.
To mount an effective defense against cyberattacks, you first need to understand what information about your organization can be gathered from public sources. This is precisely where OSINT analysis and dark web monitoring come into play.
Comprehensive OSINT techniques identify an organization's IP addresses, ports, subdomains, services, technologies in use, sensitive data, and credentials -- effectively mapping its entire attack surface.
What Are the Types?
Reconnaissance methods in an OSINT analysis fall into two categories: passive and active.
Passive methods require no interaction with the target systems and therefore cannot be detected.
Active methods involve direct interaction with target systems. This can range from advanced techniques to simple actions such as registering on an organization's website to access materials restricted to registered users.
Because active methods can be detected by security mechanisms such as IPS/IDS, they require considerably more caution to avoid alerting the target.
While analysts must tailor their OSINT techniques to the specific characteristics of each target organization, following an established methodology provides a solid foundation for effective information gathering.
The Procedure
Identifying Sources
The first phase focuses on identifying the relevant sources from which information can be obtained. These sources are documented internally according to established processes, ensuring that all details are captured and accessible for future reference.
Collecting Data
The security analyst gathers information from a variety of sources -- including social media, search engines, OSINT tools, the deep and dark web, and other channels relevant to the target organization.
Data Processing and Integration
Our experienced security analysts process the collected information into actionable insights, focusing on data points that support further enumeration.
Data Analysis
Using proven OSINT tools, the security analyst performs a systematic analysis of the processed information.
Delivery of Results
Once the OSINT analysis is complete, the findings are compiled into a report and delivered to the client or the Red Team -- for example, as the basis for an adversarial simulation.
The Best OSINT Tools
Maltego
Maltego was developed by Paterva and is included in Kali Linux (Community Edition). It enables extensive reconnaissance against targets through numerous built-in transformations. To get started, you need to register on the Paterva website.
After registration, you can create or launch a new machine to run transformations on a target. Maltego provides various built-in footprints that can be executed against the target, processing all transformations through the Maltego servers.
Typical results include domain-to-IP resolution, network block identification, AS number discovery, and location mapping. All findings are displayed as icons with detailed drill-down views. This process can be continued iteratively to gather progressively deeper intelligence. Maltego is an indispensable tool for tracing the digital footprint of any entity on the internet.
Recon-Ng
Recon-Ng is another powerful reconnaissance tool integrated with Kali Linux. Its modular architecture and usage patterns are similar to Metasploit.
You can create workspaces to organize your operations and specify target domains using the add domain command. Once domains are added, various modules become available to extract information. Modules such as bing_domain_web and google_site_web are excellent for discovering additional domains related to the original target. The bing_linkedin_cache module can identify email addresses associated with the domain -- valuable intelligence for social engineering attacks. Recon-Ng is an essential tool in every security researcher's toolkit.
theHarvester
theHarvester is another proven tool for information gathering. Built into Kali Linux, it is fast and considerably easier to use than Recon-Ng when collecting basic intelligence. The tool automatically queries sources such as Google, Bing, and PGP key servers.
Typical results include email addresses associated with the target domain, along with host and virtual host information found in search engine indexes.
Thanks to its speed and broad feature set, theHarvester is an indispensable tool for rapid initial reconnaissance.
Shodan
Shodan is widely known as the "search engine for hackers" because it provides a comprehensive overview of internet-connected devices. For security researchers, it is a goldmine for discovering exposed systems.
For example, you can find publicly accessible webcams, network cameras, and traffic control systems. Common use cases include searching for assets with open RDP ports, devices running default passwords, or systems with active VNC access.
Shodan is an excellent tool for fingerprinting connected assets and vividly demonstrates how much can be derived from publicly available information.
Google Dorks
Search engines index a wealth of information that can be leveraged for target reconnaissance. Google Dorking uses specialized search operators to surface information that standard queries cannot easily retrieve. Here are the key operators:
- Intitle: Searches for specific terms in the page title.
- Inurl: Searches for specific terms in the URL.
- Filetype: Filters results by file type.
- Ext: Identifies files with specific extensions -- particularly useful for finding files like
.logthat should not be publicly indexed. - Intext: Searches for specific text within the page content.
Practical Example: Starting from an Email Address
The following example illustrates what additional information can be gathered from a single email address. Key targets include the full name of the address owner and their employer. Beyond that, analysts attempt to identify associated social media accounts and other usernames. It is equally important to check whether the email address has appeared in known password leaks.
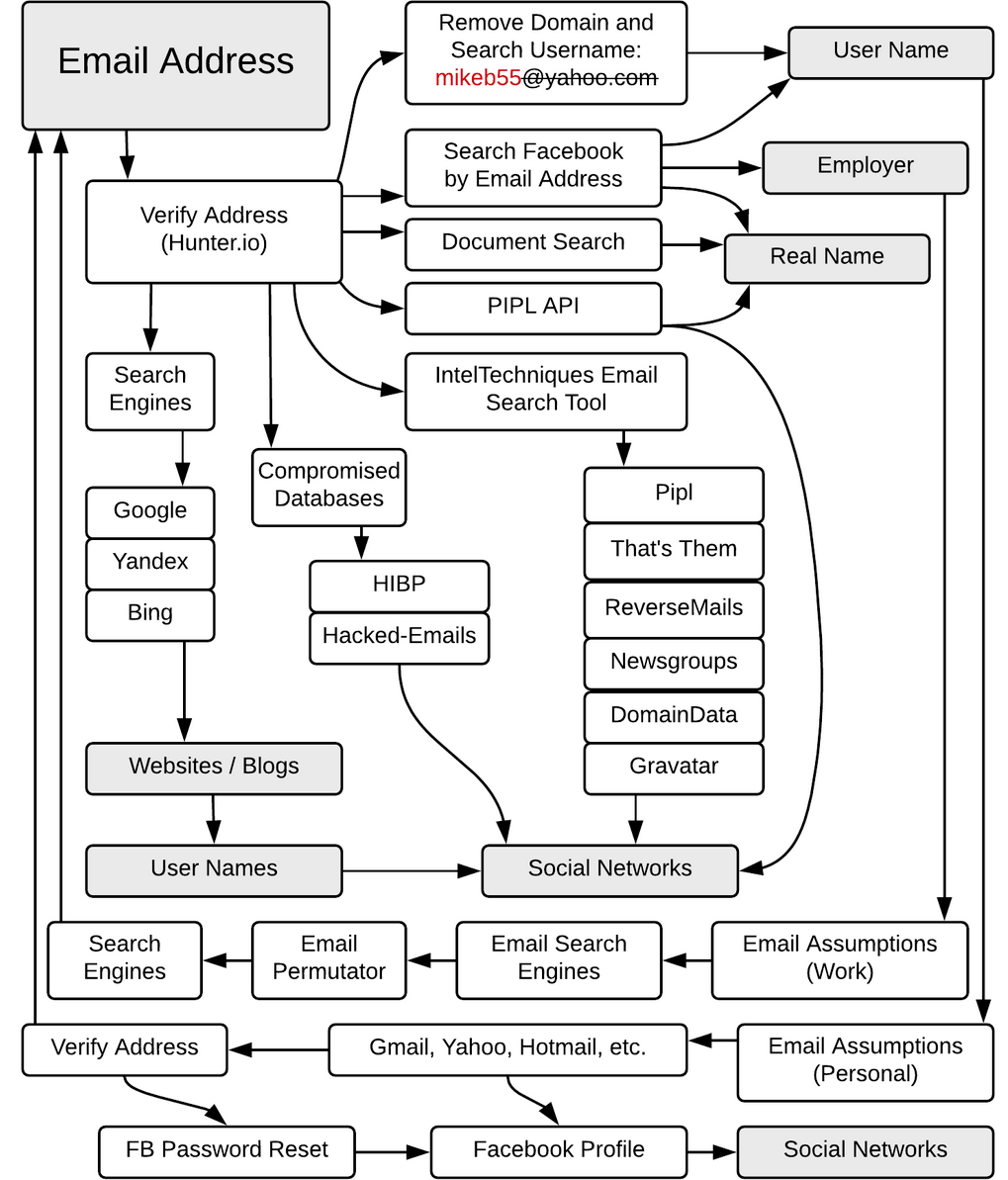
Figure 1: IntelTechniques.com OSINT Workflow Chart: Email Address
As the diagram shows, the objective is to compile as much information as possible about the person behind the email address. These findings then serve as the foundation for further OSINT research or -- given sufficient data -- for targeted attacks.
Additional workflow diagrams for parameters such as domain, username, and more can be found in this GitHub repository.
What Can You Do with the Information?
In most cases, information gathering serves as the groundwork for subsequent cyberattacks, such as:
- Social engineering, including phishing and email spoofing
- Building botnets for distributed denial of service (DDoS) attacks
- Brute-force attacks
- Doxing
- Deploying malware, including spyware, ransomware, and other forms of malicious software
This is precisely why organizations need effective information risk management that accounts for OSINT misuse. In particular, processes should be in place to respond immediately to public data leaks and software vulnerabilities.
Conclusion
In today's digital landscape, maintaining complete privacy and controlling all the information circulating about you online is virtually impossible. While you cannot manage every data point, being aware of your digital footprint is essential. In the digital age, information plays a pivotal role -- and those who know how to find it will always be one step ahead. This realization alone should motivate organizations to adopt OSINT measures as a proactive strategy for mitigating cyber risks.