The New OWASP Top 10 from 2021
There are three new categories in the OWASP Top 10 and the prioritization of some already known categories has changed.

What Is the OWASP?
The OWASP is a nonprofit organization dedicated to improving web application security. Through numerous projects (e.g. Web/Mobile Security Testing Guides, Application Security Verification Standard, and many more) as well as regular events, OWASP provides a comprehensive knowledge base that helps improve web application security. This information is backed by the extensive knowledge and experience of its contributors.
What Are the OWASP Top 10?
The OWASP Top 10 is a listing of the ten most common vulnerabilities in web applications, along with their associated risks, impact, and recommended countermeasures. The OWASP Top 10 is updated every three to four years. The list serves as a foundation for organizations to plan and implement effective security measures for their web applications. However, it is important to note that the OWASP Top 10 provides only an overview of the most common vulnerabilities and should not be treated as a mere checklist.
Comparison 2017/2021
In a nutshell, there are three new categories, and the prioritization of several existing categories has changed. In addition, some previously listed vulnerabilities have been consolidated into broader categories.
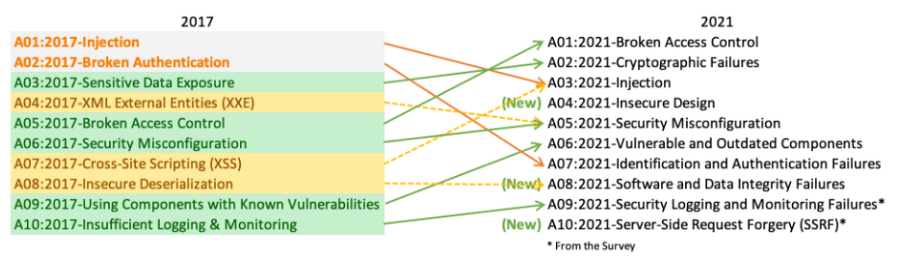
The most significant change, however, lies in how the OWASP Top 10 are meant to be viewed. While the original focus was on classifying individual vulnerabilities, the latest edition takes a much more strategic approach. Most categories are now broader than before, covering more areas. And while the Top 10 remain data-driven, they are no longer ranked primarily by frequency — instead, the focus is on exploitability and impact.
The Top 10 now also include two categories that were not derived from statistical data but rather from surveys of industry experts. This ensures that vulnerabilities which are currently less prevalent but considered critical by experts are also represented.
Broken Access Control
The new number one on the OWASP Top 10 is broken or faulty access controls. While an attacker enters through the front door in an authentication attack, a broken access control vulnerability is like an open window right next to it. This analogy illustrates the importance of implementing access controls and ensuring they function correctly. Access controls restrict user privileges and protect sensitive information from unauthorized access.
Cryptographic Failures
In the previous edition, this category was known as "Sensitive Data Exposure" — a name that describes the consequence rather than the underlying cause. The rename clarifies that the focus is on cryptographic failures, which can lead to the exposure of sensitive data. Such data includes passwords, credit card numbers, health records, personal information, and trade secrets that require special protection, particularly when subject to privacy regulations.
Injection
The injection category has dropped from first to third place, due in part to improved protections in modern frameworks and safer programming languages. In addition, cross-site scripting vulnerabilities now fall under this category as well. An application is generally vulnerable to injection attacks when user-supplied data is not properly validated, filtered, or sanitized.
Insecure Design
Insecure Design is a new risk category that focuses on vulnerabilities stemming from fundamental design flaws. It is a broad category encompassing many different types of weaknesses. The core principle is that applications must be designed with security in mind from the outset. This can be achieved through threat modeling workshops, adherence to "Security by Design" principles, and the use of proven reference architectures.
Security Misconfigurations
Security misconfigurations have risen one place compared to the previous Top 10 and now additionally encompass the former "XML External Entities (XXE)" category. These misconfigurations occur, for example, when default settings are deployed without review or adjustment.
Vulnerable and Outdated Components
Formerly known as "Using Components with Known Vulnerabilities," this category covers any software that contains vulnerabilities, is no longer supported, or is outdated. If you do not track the version numbers of your components — including all direct and indirect dependencies — and do not perform regular security scans, you are exposing yourself to significant risk.
Identification and Authentication Failures
This category evolved from the former "Broken Authentication" entry and dropped from second to seventh place. According to OWASP, it remains a significant component of the Top 10, but the wide availability of modern frameworks has substantially reduced the risk. A security risk arises when a user's identity, authentication, or session management is not handled properly, allowing attackers to exploit passwords, keys, session tokens, or implementation flaws to temporarily or permanently assume a user's identity.
Software and Data Integrity Failures
Another new addition is "Software and Data Integrity Failures," which addresses missing or inadequate integrity checks for software updates, critical data, and CI/CD pipelines. The former "Insecure Deserialization" category has also been incorporated here.
Security Logging and Monitoring Failures
The category formerly known as "Insufficient Logging and Monitoring" has been renamed to "Security Logging and Monitoring Failures" to cover a broader range of vulnerabilities. Without adequate logging and monitoring, attacks and other security breaches go undetected. A typical example is brute-force attacks, which can be identified by an unusually high number of failed login attempts within a short period.
Server-Side Request Forgery (SSRF)
Server-Side Request Forgery was added as a new category based on the industry survey. According to the OWASP survey data, the frequency of this risk was relatively low, but its potential for exploitation and impact was above average. SSRF vulnerabilities occur when a web application retrieves a remote resource without validating the provided URL. They are most common in applications where users can load content from external sources, such as webhooks, integrations, and PDF generators.
Conclusion
The current OWASP Top 10 introduces several significant changes compared to 2017. While injection vulnerabilities, long the number one entry, have dropped in the rankings, access control flaws have risen in importance. At the same time, categories are becoming broader and less specific in order to encompass a wider variety of vulnerabilities.
Nevertheless, it is important to remember that the OWASP Top 10 is not an exhaustive list of all possible security threats to web applications. Rather, it serves as a guide highlighting the most common attack vectors targeting web applications.