External vs. Internal Pentest: The Difference
Penetration tests can be performed either externally or internally, depending on the objectives of the project.
An external penetration test is the traditional and most widely used approach. It specifically targets vulnerabilities that an external attacker without valid authorization could exploit. An internal penetration test goes beyond a simple vulnerability assessment: it actively attempts to exploit identified weaknesses and determines what information is actually exposed in the process. While the objectives are identical for both variants, internal pentests typically offer significantly more attack vectors. CREST recommends in its guide to conducting an effective penetration testing program that organizations perform both internal and external tests to obtain a comprehensive picture of their security posture. In this article, we examine both approaches in detail.
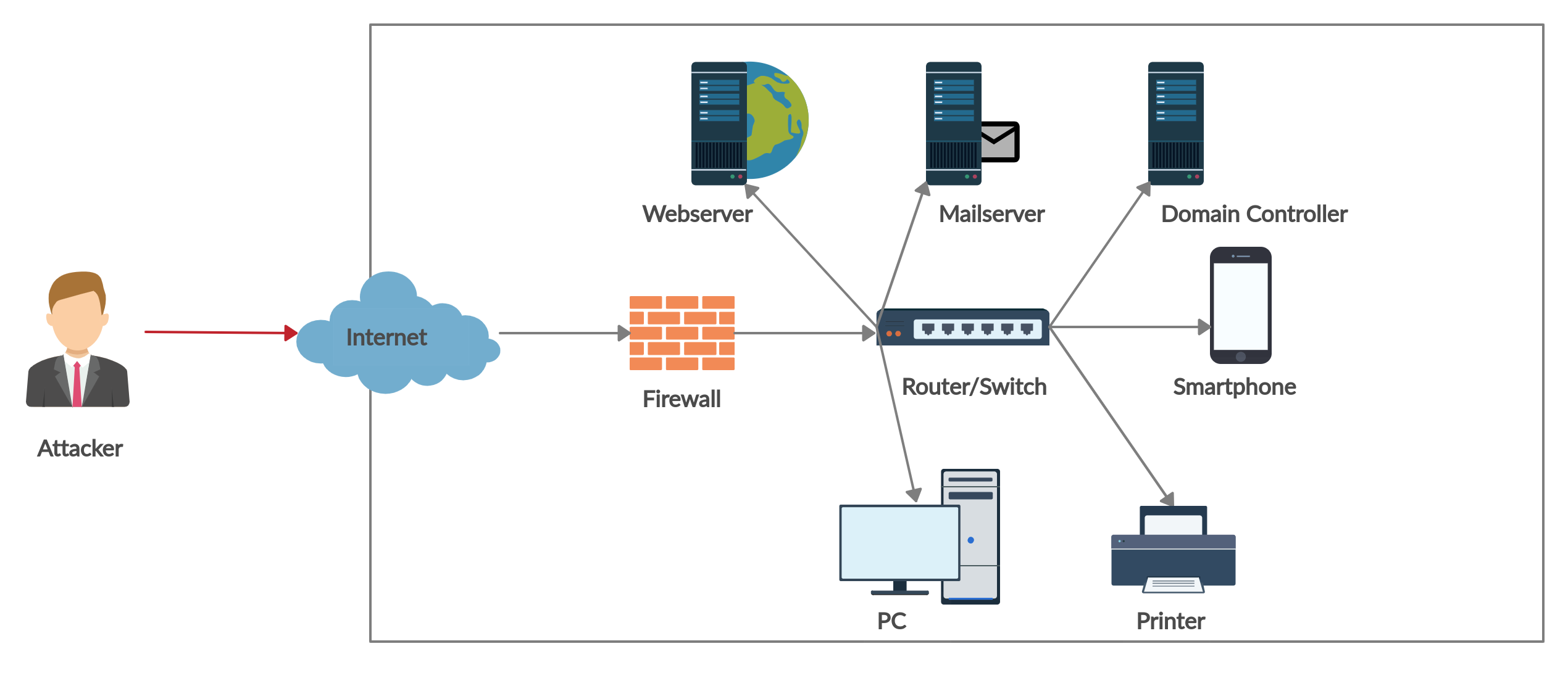
External Pentest
An external penetration test systematically examines publicly accessible endpoints to identify and eliminate potential attack surfaces for external threat actors. By actively exploiting discovered vulnerabilities, the tester determines what information is accessible to outsiders. In this way, an organization's externally facing systems and services are methodically assessed for security weaknesses.
During an external penetration test, the tester attempts to penetrate the internal network by exploiting vulnerabilities in external services. Alternatively, the tester tries to gain access to sensitive data through externally facing resources such as APIs, websites, VPNs, firewalls, mail servers, or file shares. As part of the engagement, the tester conducts thorough reconnaissance of reachable systems, gathering information on open ports, existing vulnerabilities, and general data about the organization's users that can be leveraged for password attacks.
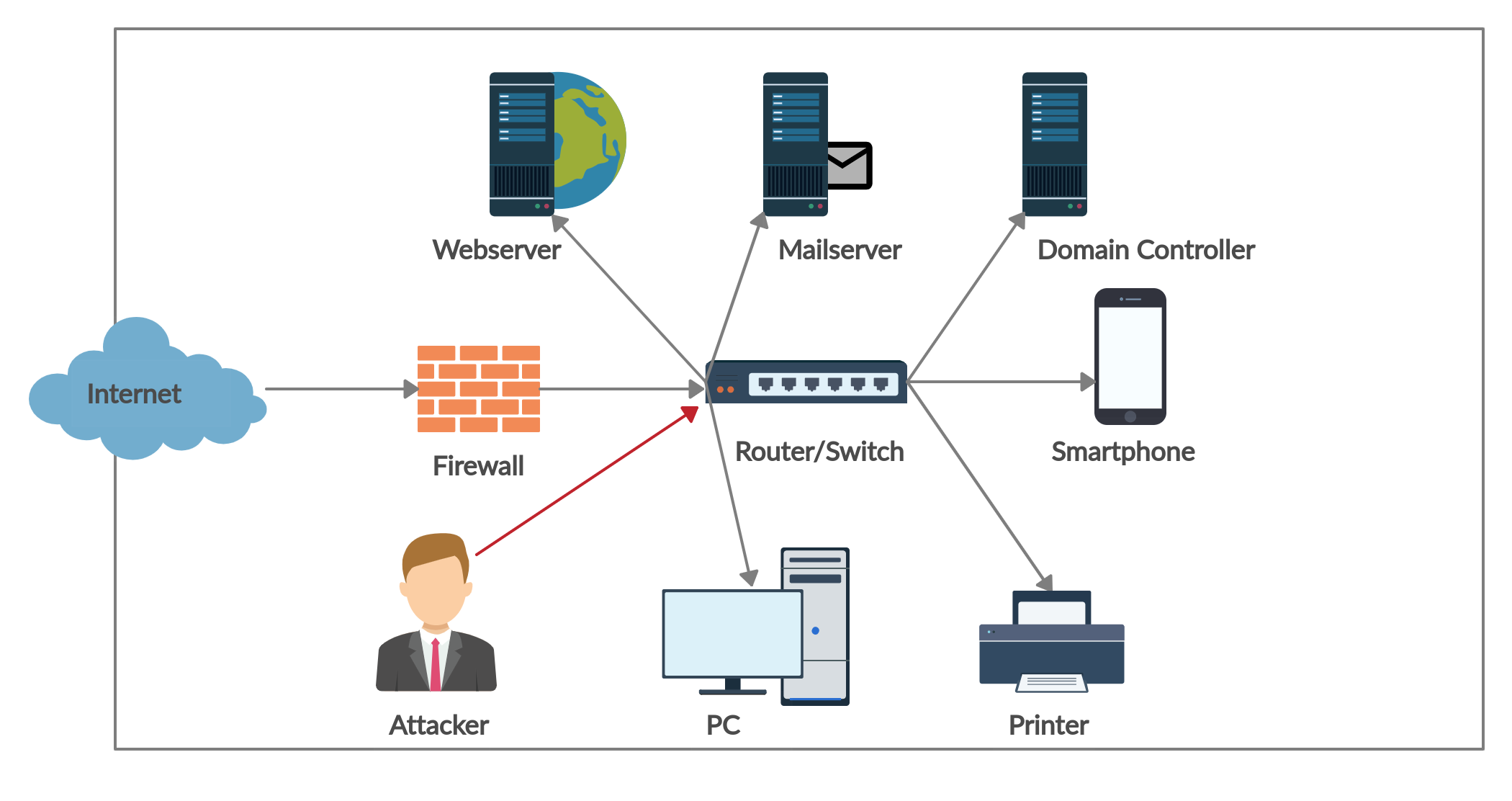
Internal Pentest
An internal penetration test takes a different approach and is often conducted following an external penetration test.
It simulates an attacker who has already gained access to the internal network. Although the methodology is similar to an external test in many respects, the key difference is that the internal test assumes the attacker already has network access -- whether through a successful external breach or insider access. The goal is to determine what an attacker with internal network access could achieve within your infrastructure.
An internal attack has the potential to cause far greater damage than an external one, since critical security mechanisms have already been bypassed and the attacker often possesses knowledge of the network architecture. This gives them a significant advantage over an external threat. The internal pentest reveals how far an attacker can move laterally through the network after a successful breach (lateral movement).
To conduct an internal penetration test, the tester either uses a pre-installed test box within the network or connects their own machine directly to the internal network. The test box is generally the preferred method, as it provides a stable testing path: tools can run indefinitely, and multiple analysts can access it simultaneously.
The test is typically considered complete once access to the domain controller has been achieved or the attacker has gained control over the organization's most critical systems and data -- depending on the scope of the engagement.
Conclusion
The importance of both external and internal penetration tests should not be underestimated. Regardless of whether the tests are performed by an internal team or an external service provider, investing in regular security assessments pays off in the long run. They help identify exploitable vulnerabilities in the network before an attacker does. Neglecting this fundamental building block of a functioning Information Security Management System (ISMS) means, at best, lacking certainty about your own security posture. At worst, a critical vulnerability goes undetected and leads to unauthorized data exfiltration.
Clear corporate policies and regular penetration tests help your organization maintain security oversight and stay one step ahead of attackers. Both test variants are essential for a well-secured network and should be conducted at least once a year. For further information, refer to the BSI's practical guide to penetration testing.